Runtime security has become one of the most critical, and most misunderstood, layers in modern application security. Most teams invest heavily in scanning code before deployment, only to discover that the threats they actually face in production look nothing like what their static tools predicted.
The reason is straightforward: attackers don’t target your source code repository. They target your running application. Zero-day exploits, code injection, privilege escalation, prompt injection against LLM integrations. These threats only exist at runtime, and they require a fundamentally different approach to detect and stop.
This guide covers what runtime security actually is, how it works at a technical level, the different types of runtime security (not just containers), how it compares to static analysis, and how modern approaches like In-App WAFs are expanding what runtime protection can do at the application layer.
What Is Runtime Security?
Runtime security is the set of technologies and practices that protect applications, systems, and data while they are actively executing. Unlike build-time security measures such as static code analysis or dependency scanning, runtime security monitors and defends live processes in real time, detecting, alerting on, and blocking threats as they occur during actual execution.
The scope of runtime security extends across the entire infrastructure stack. It can protect processes running in containers, serverless functions, virtual machines, mobile devices, and traditional server environments. What unifies all forms of runtime security is the focus on what happens after deployment: monitoring behavior, detecting anomalies, and preventing exploitation while applications are running in production.
Runtime security is essential because even well-tested, thoroughly scanned code can become compromised after deployment. New vulnerabilities are disclosed daily. Dependencies that were safe at build time may contain exploits discovered weeks later. Attackers use techniques like fileless malware, memory injection, and living-off-the-land attacks that leave no trace in static analysis. And increasingly, AI-powered applications face novel threats like prompt injection that can only be detected at the execution layer.
The question runtime security answers is one that no amount of pre-deployment scanning can: “What is actually happening inside my application right now?”
Why Runtime Security Matters
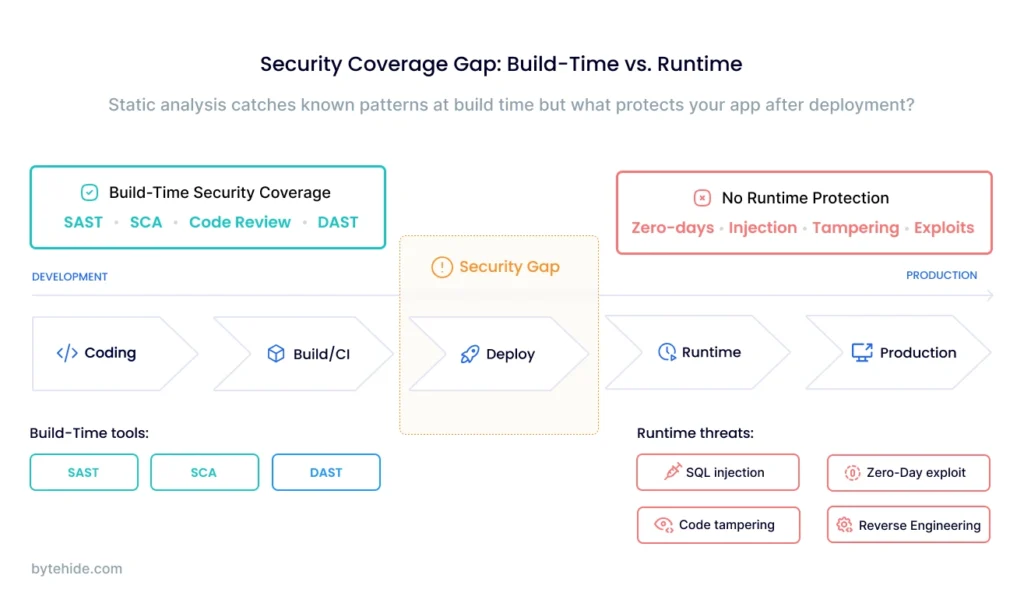
Traditional security strategies focus heavily on prevention before deployment. Static Application Security Testing (SAST) scans source code for known vulnerability patterns. Software Composition Analysis (SCA) checks dependencies against databases of known CVEs. These tools are valuable, but they share a fundamental limitation: they evaluate code at rest, not code in motion.
This creates a gap that attackers exploit consistently. Consider these scenarios that static analysis cannot address:
Zero-day exploits target vulnerabilities that haven’t been cataloged yet. No signature database catches them because no signature exists. Runtime security can detect the anomalous behavior that results from exploitation (unusual process spawning, unexpected network connections, unauthorized file access) even when the specific attack vector is unknown.
Code injection and memory corruption introduce malicious code into a running application through buffer overflows, deserialization attacks, or template injection. The malicious payload doesn’t exist in your codebase, so pre-deployment scans never see it. Only runtime monitoring can observe the injected code executing and intervene.
Supply chain attacks compromise legitimate dependencies after they’ve been vetted and deployed. The SolarWinds and Log4Shell incidents demonstrated that even trusted, widely-used libraries can become attack vectors. Runtime protection detects when a previously safe library starts behaving anomalously.
LLM and AI-specific attacks represent an entirely new category. Prompt injection, system prompt extraction, and jailbreak attempts target AI models during inference, a purely runtime activity. Organizations integrating LLMs into their applications face threats that didn’t exist two years ago and that no static tool can address.
The financial stakes are significant. According to IBM’s Cost of a Data Breach Report, the average breach cost exceeded $4.8 million in 2024, with runtime exploitation, particularly through web application vulnerabilities and compromised credentials, among the primary attack vectors. Organizations that deployed security AI and automation, including runtime detection capabilities, reduced breach costs by an average of $2.2 million compared to those without.
How Runtime Security Works
Runtime security operates through several complementary mechanisms that collectively monitor, detect, and respond to threats in live environments.
Behavioral Baselining establishes what “normal” looks like for each application, process, and workload. By learning expected patterns of system calls, network connections, file access, and resource utilization during normal operation, runtime security tools can identify deviations that indicate potential threats. A web server that suddenly spawns a shell process, a database that initiates outbound connections to unknown IPs, a container accessing files outside its expected scope: all represent anomalies detectable through behavioral analysis.
System Call Monitoring tracks the low-level interactions between applications and the operating system kernel. Every meaningful action an application takes (reading files, opening network sockets, executing processes, allocating memory) involves system calls. By intercepting and analyzing these calls in real time, runtime security can detect unauthorized actions before they complete. Technologies like eBPF (Extended Berkeley Packet Filter) enable this monitoring with minimal performance overhead by running inspection logic directly in the kernel space.
Process Isolation and Sandboxing contain running processes within defined boundaries. If one process is compromised, isolation prevents lateral movement to other processes or the host system. Container runtimes, security profiles (seccomp, AppArmor, SELinux), and application-level sandboxing all contribute to limiting the blast radius of a successful exploit.
Intrusion Detection and Prevention (IDPS) analyzes network traffic and system activity against both known attack signatures and behavioral heuristics. Modern IDPS implementations operate at multiple levels: network-based systems monitor traffic between services, while host-based systems focus on activity within individual workloads. When threats are detected, automated response capabilities can block malicious connections, terminate compromised processes, or quarantine affected containers.
Application-Level Interception monitors specific execution points within application code, such as database queries, command execution, file operations, and HTTP request handling. This is the mechanism used by RASP (Runtime Application Self-Protection) and In-App WAF solutions, providing the deepest visibility into application behavior by observing exactly how data flows through code paths.
Types of Runtime Security
One of the most common misconceptions about runtime security is that it refers exclusively to container or Kubernetes protection. In reality, runtime security spans four distinct categories, each addressing different layers of the technology stack.
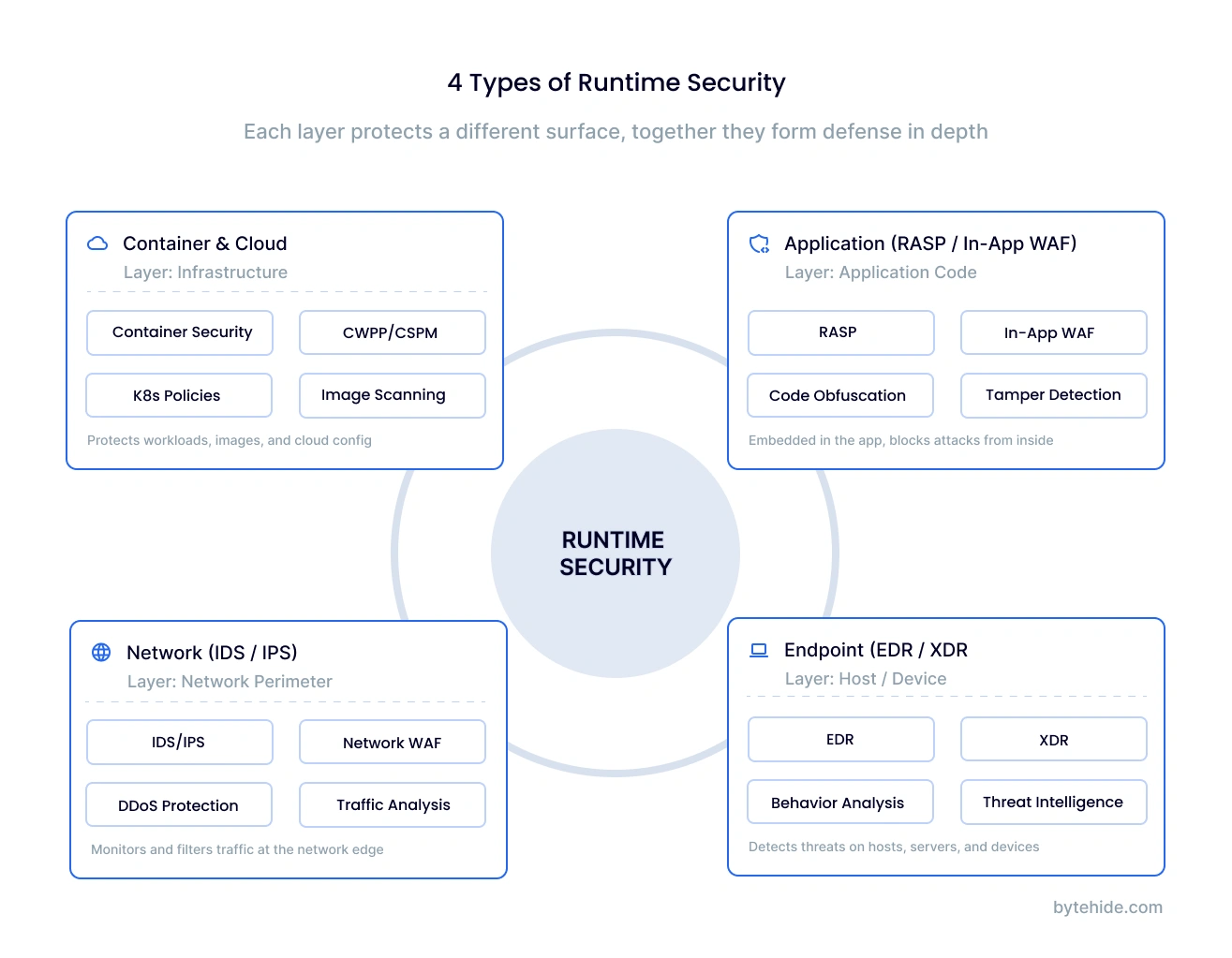
Container and Cloud Runtime Security
Container runtime security focuses on protecting workloads during execution by monitoring system calls, enforcing network policies, detecting container escapes, and preventing privilege escalation within orchestrated environments. This is the most discussed category, driven by the rapid adoption of Kubernetes, Docker, and cloud-native architectures.
Key technologies include eBPF-based sensors (like Falco), Kubernetes admission controllers, runtime scanning, and workload protection platforms. Solutions from Sysdig, Palo Alto (Prisma Cloud), Aqua Security, and Wiz operate primarily in this space.
Container runtime security is critical for organizations running microservices at scale. But it operates at the infrastructure level. It sees processes and system calls but typically lacks visibility into application-specific logic.
Application Runtime Security (RASP / In-App WAF)
Application runtime security protects the application itself during execution, operating inside the code rather than around it. This category includes Runtime Application Self-Protection (RASP) tools that instrument application runtimes, and newer In-App WAF solutions that embed lightweight security SDKs directly into application code.
Unlike container security, application runtime security understands the application’s logic. It can track how user input flows through code, determine whether a suspicious string will actually reach a vulnerable database query, and intercept threats at the exact execution point: the database driver, the system command call, the template renderer.
This category is particularly relevant for teams building web applications, APIs, and services where the attack surface is the application code itself. It also covers emerging threats like LLM prompt injection that exist entirely at the application layer. Solutions in this space include Contrast Security, Imperva RASP, and ByteHide Monitor.
Network Runtime Security
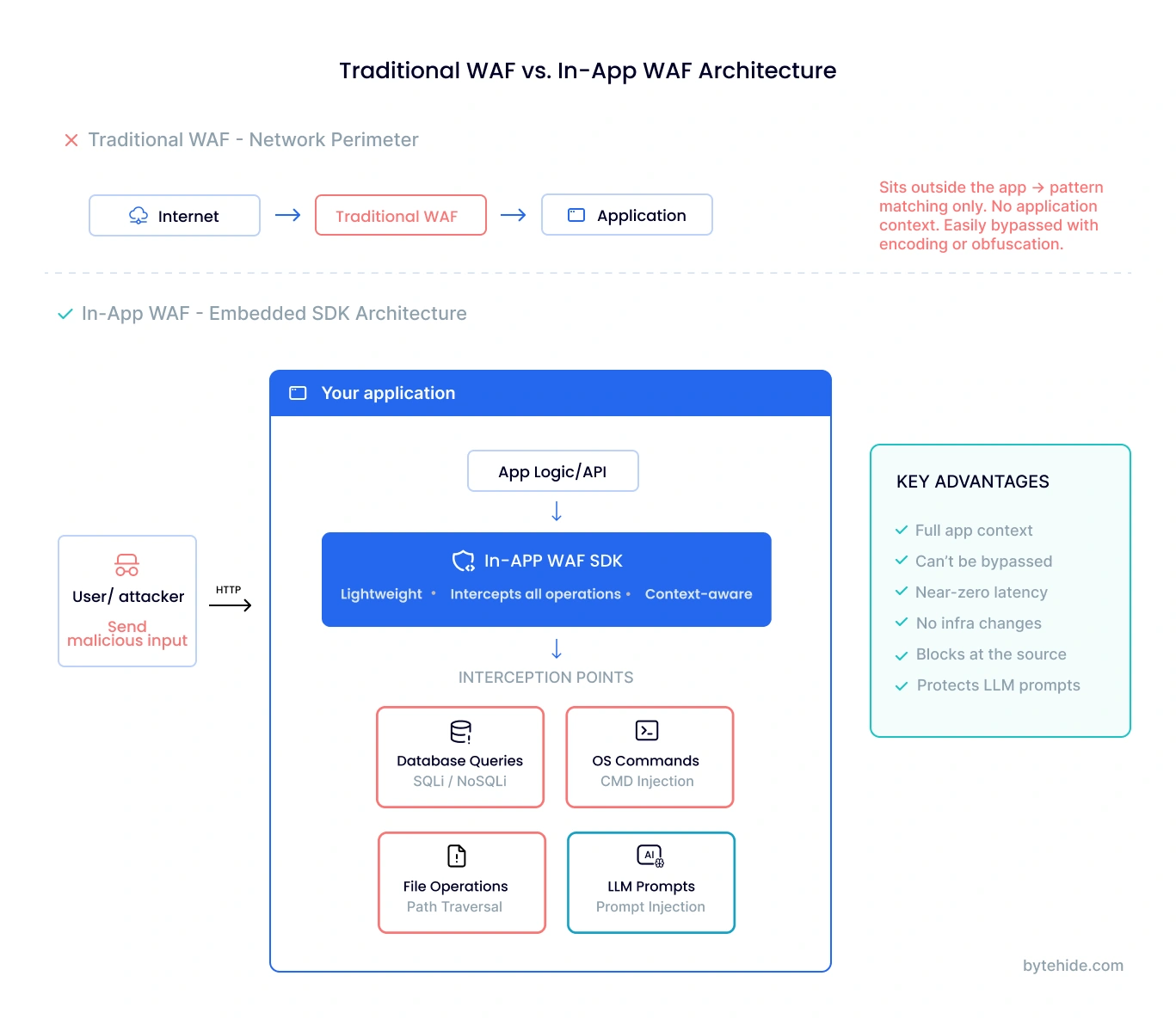
Network runtime security monitors and protects network traffic in real time. This includes traditional Intrusion Detection/Prevention Systems (IDS/IPS), Web Application Firewalls (WAFs) operating at the network perimeter, and network segmentation enforcement.
While WAFs are often categorized separately, they function as a form of runtime security. They protect applications by analyzing live traffic against rule sets. Their limitation is that they operate without application context, seeing only HTTP requests rather than understanding how those requests are processed internally.
Endpoint Runtime Security
Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) platforms protect individual devices and endpoints during operation. These tools monitor process execution, file system changes, registry modifications, and network connections on endpoints to detect malware, ransomware, and advanced persistent threats.
While endpoint security has a longer history than cloud-native runtime security, the underlying principle is identical: monitoring behavior during execution to detect and stop threats that pre-deployment measures missed.
| Type | Layer | Visibility | Best For |
|---|---|---|---|
| Container / Cloud | Infrastructure | System calls, processes, network | K8s workloads, microservices |
| Application (RASP/In-App WAF) | Application code | Data flow, queries, commands, LLM prompts | Web apps, APIs, LLM integrations |
| Network (WAF/IDS) | Network perimeter | HTTP traffic, protocols | High-volume traffic filtering |
| Endpoint (EDR/XDR) | Device / OS | Files, processes, registry | Workstations, servers, IoT |
In practice, most organizations need a combination of these types. Container security protects your infrastructure, application security protects your code, network security filters traffic, and endpoint security protects devices. The gap most organizations have today is at the application layer, where neither container tools nor network WAFs have sufficient visibility. In my experience, teams that skip application-layer protection end up relying entirely on perimeter defenses that sophisticated attackers bypass routinely.
Runtime Security vs. Static Security: Key Differences
Runtime security and static security are complementary approaches that address different phases of the software lifecycle. Understanding when each applies helps teams build effective, layered defenses.
Static security tools (SAST, SCA, secret scanning) analyze code, configurations, and dependencies without executing them. They run during development and CI/CD pipelines, catching known vulnerability patterns, insecure coding practices, and exposed credentials before deployment. Their strength is early detection: fixing a vulnerability during development is dramatically cheaper than remediating it in production.
Runtime security tools (RASP, In-App WAFs, container protection, EDR) monitor applications during execution. They detect threats that static analysis inherently cannot: zero-day exploits, behavioral anomalies, injection attacks using novel encodings, supply chain compromises activated post-deployment, and attacks targeting AI/LLM integrations.

| Dimension | Static Security (SAST/SCA) | Runtime Security |
|---|---|---|
| When it runs | During development / CI/CD | During production execution |
| What it sees | Source code, configs, dependencies | Live behavior, data flows, system calls |
| Catches | Known vulnerability patterns, misconfigs | Zero-days, injection, anomalies, exploitation |
| False positive rate | High (no execution context) | Low (confirms real behavior) |
| Performance impact | None on production | Minimal to moderate on running app |
| Coverage | Custom code + known dependencies | Entire runtime including dynamic behavior |
The ideal security posture uses both. Static tools like ByteHide Radar catch vulnerabilities early in development. Runtime tools like ByteHide Monitor protect applications in production and validate whether static findings are actually exploitable. When the two share data, with runtime confirming which static findings are being targeted by real attacks, teams can prioritize remediation with dramatically higher accuracy.
Runtime Security for Applications: The In-App WAF Approach
Traditional RASP (Runtime Application Self-Protection) was the first technology to bring runtime security to the application layer. By instrumenting application runtimes (the JVM, CLR, Node.js engine), RASP agents could observe data flow and block attacks with application context.
However, traditional RASP faced practical challenges: significant performance overhead from full instrumentation, tight coupling to specific language runtimes, complex deployment requiring JVM flags or bytecode manipulation, and limited coverage across polyglot environments.
A newer approach, the In-App WAF, addresses these limitations while retaining the core benefit of application-context awareness. Instead of instrumenting the entire runtime, an In-App WAF embeds as a lightweight SDK that intercepts specific critical operations: database queries, OS command execution, file operations, template rendering, and LLM prompt processing.
Here’s what adding application runtime security looks like in practice:
// Node.js - Add runtime protection in 3 lines
const monitor = require('@bytehide/monitor');
monitor.init({ apiKey: 'your-api-key' });
app.use(monitor.protect());
// That's it. Monitor now intercepts:
// - SQL queries before they execute (SQL injection protection)
// - OS commands before Process.exec() runs (command injection)
// - File operations before fs calls complete (path traversal)
// - LLM prompts before they reach the model (prompt injection)// .NET - Equivalent setup
using ByteHide.Monitor;
var builder = WebApplication.CreateBuilder(args);
builder.Services.AddByteHideMonitor(options => {
options.ApiKey = "your-api-key";
});
var app = builder.Build();
app.UseByteHideMonitor(); // Runtime protection activeThe In-App WAF approach offers several advantages over both traditional RASP and perimeter WAFs:
Precision with low overhead. By targeting specific interception points rather than instrumenting the entire runtime, In-App WAFs add less than 1ms per check. This makes runtime protection feasible for high-throughput APIs and latency-sensitive applications.
Application context without complexity. Like RASP, an In-App WAF sees exactly how data flows through the application. Unlike RASP, deployment is a simple SDK installation rather than bytecode manipulation or JVM configuration.
LLM and AI protection. An In-App WAF can inspect prompts before they reach language models, detecting jailbreak attempts, system prompt extraction, role manipulation, and encoded payloads. This addresses OWASP’s #1 risk for LLM applications, prompt injection, at the execution point rather than with fragile input validation patterns.
Threat intelligence integration. Beyond code-level protection, an In-App WAF can integrate threat intelligence feeds (covering 600M+ known malicious IPs, 390+ bot signatures) and enforce geo-blocking and rate limiting inside the application, independent of infrastructure setup.
For a deeper comparison of how In-App WAFs compare to traditional WAFs and RASP, see our guide on RASP vs WAF.
Runtime Security for Cloud and Containers
While this guide emphasizes application-layer runtime security, an area that most existing content underserves, container and cloud runtime security deserves recognition as the more established category.
In Kubernetes environments, runtime security typically involves deploying eBPF-based sensors on cluster nodes that monitor system calls, network connections, and process behavior across all containers. Open source tools like Falco provide real-time threat detection by matching system call patterns against configurable rule sets. Enterprise platforms from Sysdig, Aqua Security, and Palo Alto Networks (Prisma Cloud) add policy enforcement, compliance reporting, and incident response capabilities.
Key practices for cloud runtime security include enforcing least-privilege pod security policies, running containers as non-root users, implementing network policies to restrict pod-to-pod communication, using admission controllers to prevent deployment of unscanned images, and maintaining runtime scanning to detect vulnerabilities in running containers.
For organizations running both containerized infrastructure and application code, the combination of container-level runtime security (monitoring infrastructure behavior) and application-level runtime security (monitoring code execution) provides comprehensive defense-in-depth. Container security catches infrastructure-level attacks like container escapes and privilege escalation, while application security catches code-level attacks like SQL injection, prompt injection, and business logic exploitation.
Runtime Security Best Practices
Implementing effective runtime security requires more than deploying tools. These practices help maximize protection while maintaining development velocity:
Layer your defenses. No single runtime security tool covers every threat vector. Combine application-level protection (RASP or In-App WAF) with container security, network monitoring, and endpoint detection based on your architecture. The goal is overlapping coverage where a threat caught at one layer is also detectable at another.
Combine static and runtime analysis. Use SAST and SCA during development to catch what you can before deployment. Use runtime security to catch what static tools miss and to validate which static findings represent real, exploitable risks. When your runtime tool confirms a vulnerability is under active attack, that finding jumps to the top of your remediation queue.
Start in detection mode before blocking. Most runtime security tools support a monitoring or “alert-only” mode. Deploy in this mode first to understand your application’s normal behavior, tune detection thresholds, and reduce false positives before enabling automatic blocking. This is especially important for high-traffic production environments.
Enforce least privilege everywhere. Limit container capabilities, restrict process permissions, minimize network access between services, and apply the principle of least privilege to IAM roles and service accounts. Runtime security is most effective when combined with a restrictive baseline. Fewer legitimate activities mean anomalies are easier to detect.
Automate incident response. When runtime security detects a confirmed threat, the response should be automated: block the malicious request, quarantine the affected container, trigger an alert to the security team, and capture forensic data for investigation. Manual response is too slow for attacks that complete in seconds.
Monitor AI and LLM integrations. If your application integrates with language models, treat LLM interactions as security-sensitive operations. Monitor prompts for injection patterns, validate outputs before acting on them, and apply runtime protection at the inference layer. This threat category is growing rapidly and most organizations have no protection in place.
Frequently Asked Questions
What is the difference between runtime security and static security?
Static security (SAST, SCA) analyzes source code and dependencies before deployment, identifying known vulnerability patterns without executing the code. Runtime security monitors applications during execution, detecting threats like zero-day exploits, code injection, and behavioral anomalies that static analysis cannot see. Static security catches problems early in development; runtime security catches problems that only manifest in production. Most security architectures use both for comprehensive coverage.
What is cloud runtime security?
Cloud runtime security protects workloads, containers, and serverless functions while they execute in cloud environments. It typically uses eBPF-based sensors or cloud-native monitoring tools to observe system calls, network traffic, and process behavior across distributed infrastructure. Cloud runtime security is essential because cloud environments are dynamic, ephemeral, and exposed to the internet, making them prime targets for attacks that bypass traditional perimeter defenses.
How does runtime security protect against zero-day attacks?
Runtime security detects zero-day exploits not by recognizing the specific vulnerability (which is unknown), but by observing the anomalous behavior that results from exploitation. When an attacker exploits a zero-day vulnerability, the compromised process typically exhibits unusual behavior: spawning unexpected child processes, making unauthorized network connections, accessing files outside its normal scope, or executing commands it has never executed before. Runtime monitoring detects these behavioral deviations and can block or alert on them regardless of the specific exploit used.
What is RASP and how does it relate to runtime security?
RASP (Runtime Application Self-Protection) is a specific type of runtime security that operates inside the application rather than around it. RASP agents instrument the application runtime to monitor data flow, detect attacks at execution points (database queries, system commands, file operations), and block threats with full application context. RASP has evolved into newer approaches like In-App WAFs, which provide similar application-context awareness with lighter deployment models and broader coverage including LLM prompt protection.
Do I need runtime security if I already have a WAF?
A Web Application Firewall (WAF) is one form of runtime security, but it operates at the network perimeter without application context. WAFs effectively filter high-volume, known attack patterns from HTTP traffic, but they cannot see how requests are processed inside your application. Sophisticated attacks using encoding tricks, fragmented payloads, or application-specific bypasses regularly evade WAF rules. Application-layer runtime security (RASP or In-App WAF) complements a WAF by confirming whether suspicious inputs actually reach vulnerable code paths, dramatically reducing both false positives and false negatives.
What is an In-App WAF?
An In-App WAF is a lightweight security SDK that embeds directly into your application, combining the rule-based threat detection of a traditional WAF with the application-context awareness of RASP. Instead of sitting at the network perimeter, it intercepts threats at the execution point (database queries, system commands, template rendering, LLM prompts) with full visibility into how data flows through your code. The result is precise, low-overhead runtime protection that works independently of your infrastructure setup and covers threats that neither perimeter WAFs nor container security tools can detect.
Runtime security is no longer optional for organizations running production applications. Whether your stack is containerized, serverless, monolithic, or a mix of all three, threats that target running code require defenses that operate at runtime. If you want to see how application-layer runtime security works in practice, explore ByteHide Monitor.





