Obfuscate and secure all your developments with military-grade protection. Adapt it directly to your software, without the need to change your code. Automatically protect all compiled files in a fast, efficient and integrated way.


The risk of not protecting your applications
As soon as you publish your application, even on official channels, you lose full control over the environment and security of your application.
An unprotected application can be affected by many security problems.
Vulnerability detection
Damage to brand image
Cracking and Reverse-engineering
Intellectual Property (IP) Theft
Reverse engineering
If an application is not obfuscated, it is extremely easy to decompile its apk, dll, exe or jar files and access the source code with decompilers such as IDA Pro, CFF Explorer, Scylla, DnSpy, Apktool, Frida.re and many more. A non-obfuscated application is the main gateway for decompilation. Once the application is decompiled, a hacker or cracker can reverse engineer and analyze its operation.


Penetration or tampering
Reverse engineering is not everything, especially in mobile or distributed applications. Having access to source code and not having security methods in place to prevent tampering, debugging or dumping is very dangerous. Competitors or attackers can alter processes, manipulate any part of the source code or even bypass licensing systems to get into your application.
How our Application Hardening and Shielding works
ByteHide Shield is not a simple obfuscation tool, it is a service that takes care of protecting your application from compilation to when it receives attacks in an untrusted environment.

Obfuscate your application with Multi-layer protection
Protect your application with different obfuscation techniques by hiding the logic and code of your application while maintaining its functionality. The different layers combine with each other to prevent an attacker from reverse engineering, analyzing the code or obtaining confidential information.
Secure against static and dynamic attacks with In-app protection
Code obfuscation alone is not enough, applications are exposed to different types of attacks, even if you publish it through an official distribution channel. In-app protection combines different runtime protection methods, allowing your application to protect itself by detecting and mitigating attacks, even in untrusted environments.

Publish secure and robust applications, effortlessly for your developers
Shield is developer-first, integrates with the language or framework you use with a single click and requires no modifications to your code. Also it has CI/CD integration for your DevOps pipelines.
Your engineers don’t have to be security experts: configurations are simple, documentation is complete and the ByteHide platform integrates everything in one place for easy management.
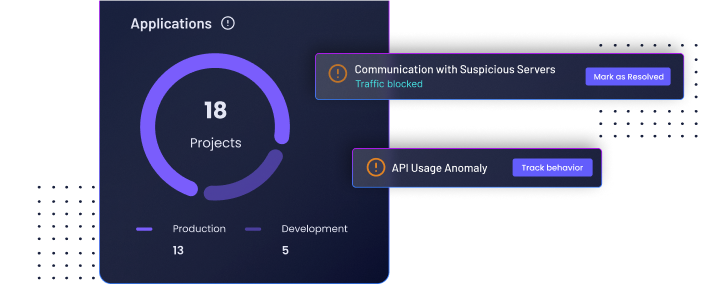
Monitor your application and receive AI real-time insights
Get control of your application, receive alerts about security warnings on the devices where your application is located. Get reports on application integrity and receive insights on blocked threats.
This allows you to keep your security team up to date, manage security in an active and preventive way. You will be able to expand the possibilities of reacting to an attack.

Obfuscate your application with Multi-layer protection
Protect your application with different obfuscation techniques by hiding the logic and code of your application while maintaining its functionality. The different layers combine with each other to prevent an attacker from reverse engineering, analyzing the code or obtaining confidential information.
Secure against static and dynamic attacks with In-app protection
Code obfuscation alone is not enough, applications are exposed to different types of attacks, even if you publish it through an official distribution channel. In-app protection combines different runtime protection methods, allowing your application to protect itself by detecting and mitigating attacks, even in untrusted environments.

Publish secure and robust applications, effortlessly for your developers
Shield is developer-first, integrates with the language or framework you use with a single click and requires no modifications to your code. Also it has CI/CD integration for your DevOps pipelines.
Your engineers don’t have to be security experts: configurations are simple, documentation is complete and the ByteHide platform integrates everything in one place for easy management.
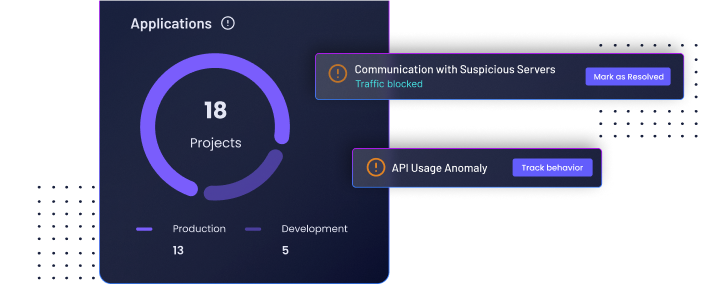
Monitor your application and receive AI real-time insights
Get control of your application, receive alerts about security warnings on the devices where your application is located. Get reports on application integrity and receive insights on blocked threats.
This allows you to keep your security team up to date, manage security in an active and preventive way. You will be able to expand the possibilities of reacting to an attack.
Benefits of obfuscation and In-app protection with Shield
Never worry about reverse engineering again. Focus on your business and automate your software security.
Protect your applications easily
An obfuscator together with In-app protection is the most complete tool you will find to protect your applications easily and without the need to be an expert in encryption or cybersecurity. Keep competitors and hackers away from your app’s source code.

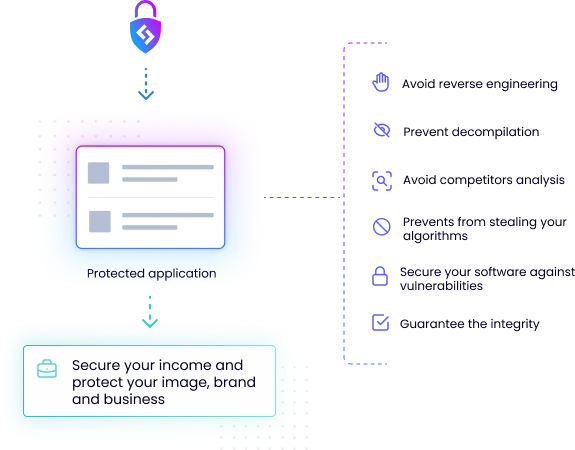
Avoid decompilation and reverse engineering
Hardening and shielding applications will guarantee their integrity by keeping them functionally identical. It will prevent any attacker from cracking or reverse engineering your application and ensure that they cannot access the source code by decompiling it.
ACCESSIBLE ADVANCED TECHNOLOGY
Why choose ByteHide
ByteHide Shield is an advanced and flexible obfuscation service, an automated way to secure application source code in the same build process.
It is designed to integrate with a single click and automate the security of your applications. No configurations or requirements needed!

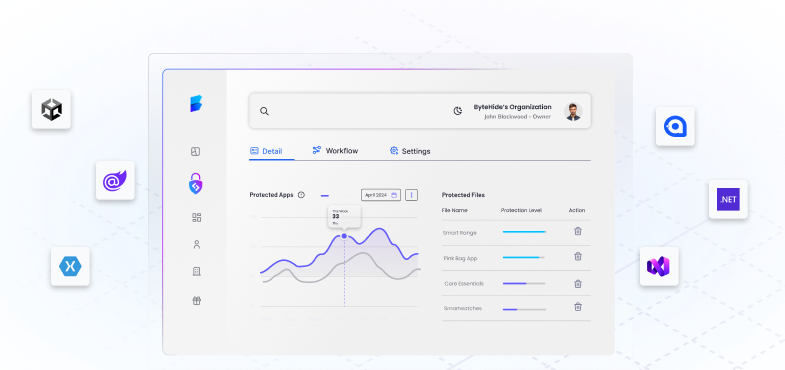
Centralize the security of your applications, manage everything in one place
Shield is not an isolated tool, difficult to configure and not integrated with anything. It is a service of the ByteHide platform that allows you to centralize user and role management, integrate your CI/CD processes, integrate with other tools, your own environments and manage configurations in a single place. Shield should not be configured in isolation, just activate it in your ByteHide account and integrate it.

Configure, integrate and get your app ready for distribution in seconds
You don’t need experts, you can turn your application into a self-protecting application with ByteHide Shield. Both Android, IOS and desktop apps for Mac and Windows can be protected in a few seconds with our integration tool. Once protected it can be automatically and securely distributed.

Your application security always up to date
Being an obfuscator on the ByteHide platform, you always have the latest and new updates, ensuring that your applications are protected with the latest technology. In addition, you derive the processing power in our infrastructure, keeping your application secure throughout the process as we do not store any data.
Just because you can integrate it yourself does not mean that you are alone
- What should you do if you receive an alert that your application is under attack?
- Should you apply control flow protection before or after injecting a debugger detection?
- Should you apply any preventive action if your application is running on a rooted device?
Just let us help you, use our technical support of cybersecurity and reverse engineering experts to solve your doubts. Even configure it for you, in a guaranteed minimum of time.
ACCESSIBLE ADVANCED TECHNOLOGY
Why choose ByteHide
ByteHide Shield is an advanced and flexible obfuscation service, an automated way to secure application source code in the same build process.
It is designed to integrate with a single click and automate the security of your applications. No configurations or requirements needed!

Centralize the security of your applications, manage everything in one place
Shield is not an isolated tool, difficult to configure and not integrated with anything. It is a service of the ByteHide platform that allows you to centralize user and role management, integrate your CI/CD processes, integrate with other tools, your own environments and manage configurations in a single place. Shield should not be configured in isolation, just activate it in your ByteHide account and integrate it.

Configure, integrate and get your app ready for distribution in seconds
You don’t need experts, you can turn your application into a self-protecting application with ByteHide Shield. Both Android, IOS and desktop apps for Mac and Windows can be protected in a few seconds with our integration tool. Once protected it can be automatically and securely distributed.

Your application security always up to date
Being a cloud obfuscator on the ByteHide platform, you always have the latest and new updates, ensuring that your applications are protected with the latest technology. In addition, you derive the processing power in our infrastructure, keeping your application secure throughout the process as we do not store any data.
Just because you can integrate it yourself does not mean that you are alone
- What should you do if you receive an alert that your application is under attack?
- Should you apply control flow protection before or after injecting a debugger detection?
- Should you apply any preventive action if your application is running on a rooted device?
Just let us help you, use our technical support of cybersecurity and reverse engineering experts to solve your doubts. Even configure it for you, in a guaranteed minimum of time.
Features to help your team succeed
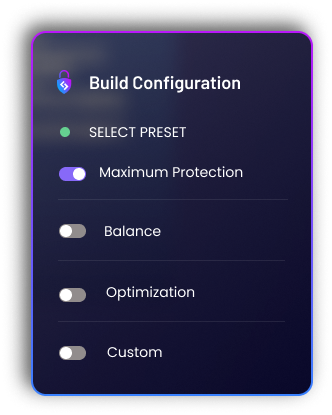
Enterprise-grade obfuscation, easy for you
Select and configure the protections easily. The protections are multi-layered but you don’t have to worry about the compatibility between them, automatically the compatibility settings will be applied and balanced for your specific application. Being polymorphic protections, a single configuration will protect your application differently each time, making the security level very high.


Cross-platform availability
You can create a project for each programming language, framework, or platform. This allows you to configure the protection of all your applications easily and define configurations for each of them. As the platform is adapted to the language and specific needs, you will be able manage all your projects from the ByteHide platform only.
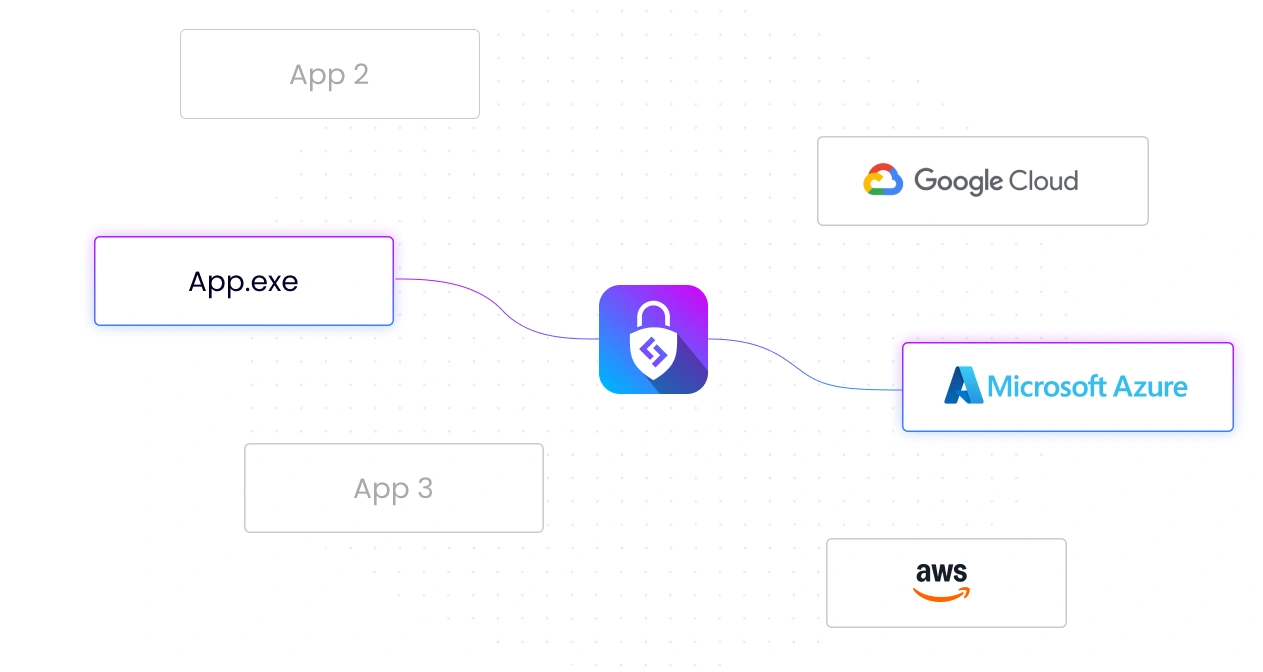
Flexible and integrable service
No matter what IDE developers use, deployment platform or end servers. Shield offers API integrations and SDKs per language and platform, as well as integrations with cloud services such as Azure, Amazon Web Services, Google Cloud and more. No configurations are required, integrate Shield with a click.

Monitor your application in end-user environments
View usage and security statistics from the web dashboard and receive alerts and notifications when security-related events occur in your application. Also receive weekly or monthly reports on your application’s current and long-term security and risk. In addition, you control environments, disable execution on rooted devices, virtual machines or enable real-time detection of hacking tools.
Compliance and regulations
Add robust data protection controls to support compliance with regulations such as PSD2, GDPR, CCPA, PCI and others. Meet compliance requirements with ByteHide Shield.



Support GDPR compliance
The GDPR requires two special articles for the protection of mobile applications. Comply with Article 25: Data protection by design and by default and Article 32: Security of processing by using Shield in your applications.

PCI developer guidelines
There are different requirements listed in the PCI regulations for accepting payments in mobile applications. Shield helps you cover several of these regulations.
Shielding to support PSD2
For mobile banking applications, the security requirements set out in DSP2 point to the need for protection against known and unknown attacks against mobile applications. Shield covers the regulations for your company.
Using ByteHide Shield to obfuscate applications in their compilation
Frequently asked questions about obfuscation and applications protection
What is obfuscation?
The term obfuscation is commonly used in cybersecurity to refer to making something difficult to read or understand. In the programming world, when the source code of an application is obfuscated it means that it is “modified” using renaming techniques and cryptographic algorithms to encrypt and harden. This obfuscation process is done to prevent the application from being reverse engineered and decompiled to avoid a wide variety of attacks.
Why should I obfuscate my applications?
Just as code once programmed becomes an application, that application can be reversed to get the source code of it. If the source code of this application is accessed without protection, shielding or obfuscation, its operation can be analyzed. This opens up many possibilities for attacks, both cracking and reverse engineering.
If an attacker accesses the source code of your application without obfuscation, he can actually completely modify its operation. In addition, it can steal intellectual property (IP) and cause a very bad image for a business or company, not to mention that there may be sensitive data (such as customer data, passwords or unencrypted database connections) that the attacker or competitor can easily access.
How can I obfuscate my applications?
There are actually many ways to obfuscate an application, from encrypting sensitive parts of the code, to replacing classes or variable names, to anti debugging or anti tampering techniques. All this is only useful if the person in charge of performing the obfuscation has advanced knowledge in logarithmic mathematics, encryption and cryptography. If not, anyone with a minimum knowledge in reverse engineering could reverse all the protections and access the source code. In that case the favorite and most powerful option is to use an obfuscator.
What is an obfuscator?
An obfuscator is a tool that analyzes your application, detects sensitive parts and through different obfuscation techniques increases the security of an application. The obfuscator converts the source code into code that is practically impossible to read by a human, but at the same time maintains its functionality at 100%. The recommendation we always make is the ByteHide Shield obfuscator because it offers military-grade encryption with super-simple preconfigurations. Literally anyone could protect their application with ByteHide Shield in 3 clicks!