Most teams deploy a WAF, enable the default ruleset, and consider the job done. Then three months later they’re drowning in false positives, blocking legitimate users, or discovering that a real attack slipped through because the attacker used URL encoding the rule didn’t account for.
Web application firewall rules are not a set-and-forget configuration. They require an understanding of how the detection model actually works, a disciplined approach to testing, and an honest assessment of what rules can and cannot protect against. This guide covers all three: from the internal mechanics of WAF rule evaluation to the structural limitations that no amount of tuning can overcome.
If you’re responsible for configuring your organization’s WAF, or you’re evaluating whether your current setup is actually protecting your application, this is what you need to know.
How WAF Rules Actually Work
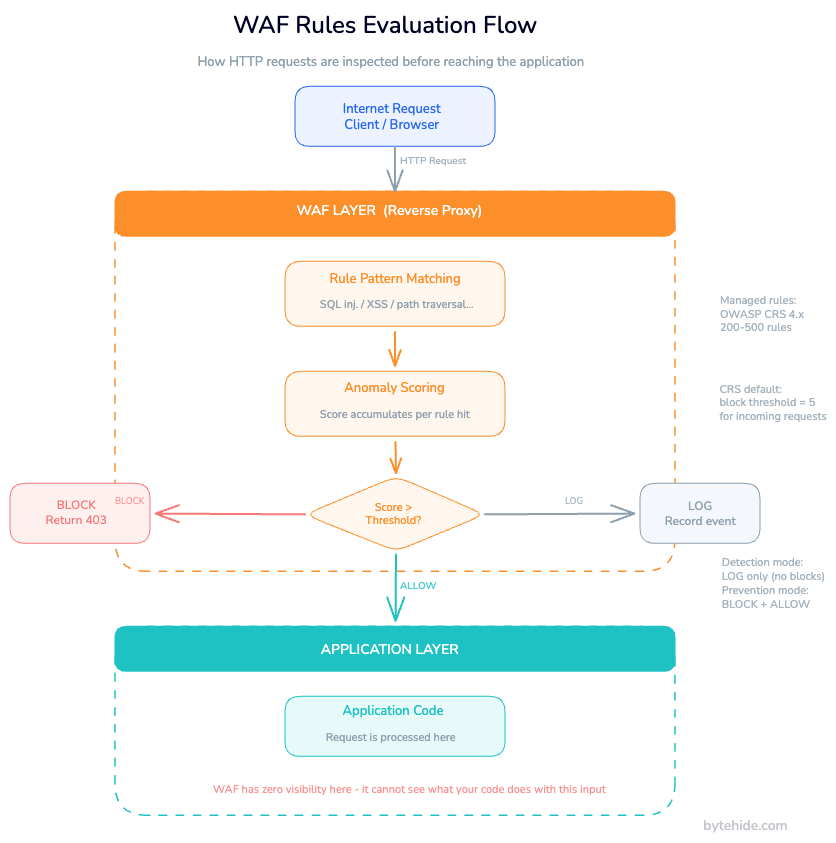
A web application firewall sits between your application and the internet, typically as a reverse proxy. Every incoming HTTP and HTTPS request passes through the WAF before reaching your server. The WAF evaluates each request against a set of rules and decides whether to allow it, block it, log it, or challenge the requestor.
The key word is “evaluate.” A WAF does not understand your application. It inspects the raw HTTP request (the URL path, query parameters, headers, cookies, and body) and looks for patterns that match known attack signatures. If a request contains a pattern that matches a SQL injection rule, the WAF flags it. Whether that pattern would actually cause harm depends entirely on what your application does with that input, and the WAF has no way to know.
The negative and positive security models
WAF rules operate on one of two models, or a hybrid of both.
The negative security model (blocklist) defines what traffic is not allowed. Rules specify patterns associated with known attacks: SQL injection strings, XSS payloads, path traversal sequences, and so on. Anything that doesn’t match a rule is allowed through. This is the dominant model in practice because it’s easier to deploy: you don’t need to know every valid request pattern upfront.
The positive security model (allowlist) defines what traffic is allowed. Only requests that match approved patterns can proceed. Everything else is blocked by default. This model has fewer false negatives but requires significantly more upfront work and ongoing maintenance as your application evolves.
Most production deployments use a hybrid: managed rules (negative model) for broad attack coverage, combined with custom rules that allowlist specific trusted traffic.
Anomaly scoring
Pure rule matching, where a single rule match causes an immediate block, generates unacceptable false positive rates in production. Modern WAF implementations use anomaly scoring instead.
Rather than blocking on any single rule match, the WAF assigns a score to each rule hit. A request accumulates score as it matches multiple rules. When the total anomaly score crosses a threshold, the WAF blocks the request. A request that matches one low-severity rule might score 3 points; a request that triggers five high-confidence rules might score 40.
OWASP’s Core Rule Set (CRS) uses this model. The default blocking threshold is 5 for incoming requests and 4 for responses. You can adjust these thresholds during tuning to trade off between security coverage and false positive rate.
Detection mode versus prevention mode
Every WAF supports two operational modes. Detection mode logs rule matches but does not block any traffic. Prevention mode actively blocks requests that meet the blocking criteria.
Start in detection mode. Always. Running in detection mode for 1–2 weeks before enabling prevention gives you a baseline: which rules fire on legitimate traffic, which endpoints generate the most noise, which thresholds need adjustment. Switching to prevention mode on a fresh WAF deployment without this baseline guarantees a wave of blocked legitimate requests and frustrated users.
Types of WAF Rules
WAF rules fall into four broad categories, each serving a different purpose in your security configuration. Understanding the role of each type is the prerequisite to configuring them correctly.
Managed rules (OWASP CRS and vendor rule sets)
Managed rules are maintained by the WAF provider or a standards body and updated as new attack patterns emerge. They’re the starting point for any WAF deployment.
The OWASP Core Rule Set is the most widely deployed open standard for WAF rules. CRS 4.x (released 2024) represents the first major update in eight years and includes improved detection for modern attack vectors, better false positive handling, and updated coverage for the OWASP Top 10. If your WAF uses the older 3.x CRS, upgrading to 4.x is worth evaluating.
ModSecurity was the traditional engine for CRS-based rule evaluation. It reached end-of-life in 2024. If your WAF depends on ModSecurity, consider migrating to Coraza WAF, an actively maintained open-source WAF engine with full CRS compatibility.
Most cloud WAF providers maintain their own managed rule sets that extend CRS with threat intelligence feeds, vendor-specific vulnerability patches, and bot protection. These are updated more frequently than CRS and require less operational effort to maintain. The tradeoff is less transparency into what individual rules do and more vendor dependency.
Custom rules
Managed rules protect against generic attack patterns. Custom rules protect your application’s specific attack surface.
Custom rules let you define logic based on any request attribute: path, method, headers, query parameters, IP ranges, geographic origin, user agent, request rate, and more. Common use cases include:
- Restricting admin endpoints to internal IP ranges
- Blocking specific user agents associated with scrapers or scanners
- Enforcing rate limits on authentication endpoints
- Blocking requests from countries you don’t operate in
- Protecting API endpoints that require specific headers
Here’s a generic custom rule structure, which most WAF platforms follow in some variant:
{
"rule_id": "custom-001",
"name": "Restrict admin access to internal networks",
"priority": 10,
"conditions": [
{
"field": "request.path",
"operator": "startsWith",
"value": "/admin"
},
{
"field": "request.client_ip",
"operator": "notInCIDR",
"value": ["10.0.0.0/8", "172.16.0.0/12", "192.168.0.0/16"]
}
],
"action": "block",
"response_code": 403,
"log": true
}Priority matters. Custom rules are evaluated in priority order, and the first matching rule wins. Set administrative access rules and IP allowlists at high priority (low number) so they evaluate before managed rules. This prevents your own internal monitoring tools from getting blocked by CRS rules.
Rate limiting rules
Rate limiting restricts how frequently a client can make requests within a time window. These rules protect against brute force attacks on login endpoints, credential stuffing, account enumeration, and API abuse.
A well-configured rate limiting rule specifies the identifier (IP address, session token, API key, or user account), the time window, the threshold, and the action when the threshold is crossed. Temporary blocking with exponential backoff works better than permanent blocks for most use cases it stops automated attacks without permanently blocking legitimate users who hit a spike.
Rate limiting rules on authentication endpoints should trigger at conservative thresholds. Ten failed login attempts in 60 seconds is already unusual for a human user.
IP, geo, and bot rules
These rules operate on request origin rather than request content.
IP blocklists based on threat intelligence feeds can block known malicious IP ranges automatically. These feeds are updated continuously and can block a substantial portion of automated attack traffic before it reaches your application layer.
Geo-blocking restricts traffic to countries or regions you operate in. It reduces attack surface but requires care: VPN usage, CDN exit nodes, and legitimate users traveling internationally can all trigger false positives.
Bot management rules categorize requests as legitimate bots (search engine crawlers, uptime monitors), known bad bots (scrapers, vulnerability scanners), or unknown. For applications where bot traffic affects performance or revenue, enabling bot management at the WAF layer reduces load on your application while protecting against automated abuse.
Configuring WAF Rules Step by Step
The following process applies regardless of which WAF platform you’re using.
Step 1: Enable detection mode. Start with the WAF running in log-only mode. No traffic should be blocked at this stage. The goal is to collect data.
Step 2: Enable managed rules. Turn on the OWASP CRS or your vendor’s equivalent managed rule set. Keep all rules at their default actions (log in detection mode, block in prevention mode) to start. Don’t tune before you have data.
Step 3: Collect logs for at least one week. Review the WAF log, not just the traffic log. The WAF log shows which specific rules matched, what the matched content was, and the anomaly score accumulated per request. Identify rules that consistently fire on legitimate traffic.
Step 4: Create rule exclusions. For rules that generate consistent false positives on legitimate requests, create targeted exclusions. Exclusions should be as specific as possible: exclude a rule for a specific path, or exclude a specific request field from a rule’s scope, rather than disabling the rule entirely. But don’t create exclusions preemptively. Only add them when you have log evidence that a specific rule is causing false positives.
Step 5: Add custom rules. With managed rules tuned and exclusions in place, add custom rules for your application-specific requirements: admin IP restrictions, API rate limiting, bot management.
Step 6: Switch to prevention mode. Enable active blocking. Monitor closely for the first 24–48 hours. Have a rollback plan.
Step 7: Establish a maintenance cadence. WAF configuration degrades over time as your application changes. Every significant application release should trigger a WAF rule review. New endpoints, new request formats, and new authentication mechanisms all affect what constitutes legitimate traffic.
Testing WAF Rules Without Breaking Your Application
Testing is the step most teams skip, which is why WAF false positives are so common. Before enabling prevention mode, verify that your rules block what they should and allow what they should.
Passive mode testing
The most production-safe testing method is passive observation. Run the WAF in detection mode for a representative traffic period of at least a full business cycle, including peak hours, off-hours, and any batch processing windows that generate unusual traffic patterns.
Review rules that triggered frequently on legitimate traffic. For each one, examine the matched content: what was in the request that matched the rule? Is this a genuine false positive (legitimate traffic incorrectly flagged) or is it ambiguous traffic that deserves inspection?
Attack payload testing
To verify your rules actually block attacks, test against known attack categories. For each attack class your WAF claims to protect against, generate representative test requests and confirm the WAF blocks them.
Use dedicated WAF testing tools like GoTestWAF, which simulates attack payloads across multiple categories and measures detection rates. Testing manually with individual payloads works for spot checks but doesn’t give you systematic coverage.
When testing in production environments, use your own infrastructure. Generate test requests from IP ranges you control, against endpoints you own, during low-traffic windows. Always test in detection mode first: confirm detection before you confirm blocking.
This table shows what to verify for each attack category:
| Attack Type | Test Method | Verify WAF Response |
|---|---|---|
| SQL injection | Parameterized injection strings in query params and body | Block / anomaly score accumulation |
| Cross-site scripting (XSS) | Script tags and event handlers in input fields | Block |
| Path traversal | Directory traversal sequences in file path parameters | Block |
| Command injection | Shell metacharacters in command-accepting parameters | Block |
| SSRF | Requests targeting internal IP ranges and metadata endpoints | Block |
| Rate limiting | Burst requests above threshold from single IP | Rate limit action |
| Geo-blocking | Requests from IP addresses in blocked regions | Block |
Canary endpoints
Create one or more decoy endpoints in your application that no legitimate user or service should ever access. Examples: /admin-test, /api/debug/internal, /config/status.
Configure these endpoints to never return valid responses, and set your WAF to alert immediately on any access. Any request to a canary endpoint is a strong signal of reconnaissance or exploitation attempt. These are particularly useful for detecting attackers who are mapping your application’s attack surface before launching a targeted attack.
Optimizing WAF Rules: Reducing False Positives
Why false positives happen
False positives aren’t a configuration mistake. They’re a structural consequence of how rule-based WAF detection works.
The WAF inspects HTTP request content and matches it against patterns. A parameter value that looks like a SQL injection attempt triggers a SQL injection rule, regardless of whether that parameter is ever used in a database query. The WAF can’t know. It doesn’t have visibility into your application code. It sees the request, not what happens when your application processes it.
I’ve seen teams spend weeks tuning WAF rules for a single endpoint that accepted rich text input from users. The endpoint processed the input as a document, stored it in a file, and never passed it to a database. The WAF’s SQL injection rules fired constantly on legitimate content. The correct fix was a targeted rule exclusion for that specific field and path, not broader rule adjustments that would reduce protection everywhere else.
This is the fundamental constraint: pattern matching on HTTP content is a probabilistic approach. A rule that detects 99% of real SQL injection attempts with a 2% false positive rate sounds reasonable until you’re running 100,000 requests per day and blocking 2,000 legitimate users.
Tuning strategies
Rule exclusions by field. If a specific request field consistently generates false positives (a JSON body field that contains structured data the WAF misidentifies as injection), create an exclusion scoped to that field and the relevant rule ID. Most WAF platforms support exclusions at this granularity.
Anomaly score threshold adjustment. Increasing the blocking threshold reduces false positives at the cost of allowing some low-confidence attacks through. This is a tradeoff, not a fix. If you’re increasing thresholds to suppress noise, the underlying issue is usually that managed rules are too broadly tuned for your specific application.
Allowlists for trusted sources. Internal services, monitoring agents, and partner integrations often generate traffic patterns that look anomalous. Allowlisting known IP ranges or API keys for these sources before rule evaluation reduces noise without compromising protection for external traffic.
Endpoint-scoped rules. Your public-facing web frontend and your internal API have very different expected traffic patterns. Configuring separate rule sets for different application sections lets you tune aggressively for high-risk endpoints (authentication, file uploads, admin panels) without loosening protection across the board.
WAF Rules Coverage for OWASP Top 10
WAF rules provide meaningful coverage for some OWASP Top 10 categories and essentially no coverage for others. Understanding this distinction prevents overconfidence in your WAF deployment.
| OWASP Category | WAF Rule Coverage | Structural Limitation |
|---|---|---|
| A01 Broken Access Control | Partial | WAF can’t evaluate authorization logic; only rule-based access (IP, path) |
| A02 Cryptographic Failures | None | Encryption/config layer, not request content |
| A03 Injection (SQLi, CMDi, XSS) | High | Pattern-based; encoding evasion can bypass. No code-level context |
| A04 Insecure Design | None | Architectural flaw, not detectable in requests |
| A05 Security Misconfiguration | Partial | Can block HTTP method exploits; can’t detect misconfigured services |
| A06 Vulnerable Components | None | Dependency layer, not visible in requests |
| A07 Auth/Session Failures | Partial | Rate limiting on login; can’t verify session validity |
| A08 Software Integrity Failures | Low | Can detect some serialization payloads; limited general coverage |
| A09 Logging/Monitoring Failures | None | Not a request-layer problem |
| A10 SSRF | Partial | Can block requests to private IP ranges if configured; DNS rebinding bypasses this |
The pattern here is consistent: WAF rules work well for attack categories where the malicious intent is visible in the HTTP request content. They provide limited or no protection for attack categories that depend on application logic, configuration state, or behavior that isn’t observable at the HTTP layer.
Where Rule-Based WAF Hits Its Ceiling
WAF rules are a valuable security layer. They also have a structural ceiling that tuning cannot overcome.
Encoding and obfuscation bypass. Attackers who understand how WAF rules work can craft payloads that encode or fragment the attack across multiple requests in ways that evade pattern matching. Double URL encoding, base64 encoding, Unicode normalization differences, and HTTP parameter pollution are all techniques used to bypass rule-based detection. The WAF evaluates the raw HTTP content; the backend application decodes it before processing. That decoding gap is permanent.
No application context. The same parameter value can be completely safe in one endpoint and critical in another. A parameter passed to a text rendering function behaves differently from the same parameter passed to a database query. The WAF sees the parameter, not the destination. This means any rule aggressive enough to catch all injection attempts will generate false positives on legitimate traffic that happens to look similar.
Zero post-request visibility. If an attack succeeds (the attacker found a bypass, or the rule was not tuned for that specific variant), the WAF has no information about what happened inside the application. No line of code, no database query, no function call. Your WAF log shows the request was allowed. It tells you nothing about the impact.
These aren’t problems with any specific WAF product. They’re inherent to the architecture of perimeter-based pattern matching. A security layer that operates on HTTP content cannot have visibility into code execution. The complete breakdown of WAF bypass techniques and limitations covers specific evasion methods in more depth.
Beyond WAF Rules: Context-Aware Runtime Protection
If the root problem is that the WAF doesn’t see your code, the logical response is protection that does.
In-App WAF operates inside your application, at the code execution layer. This is a form of runtime protection that works where HTTP inspection cannot reach. Instead of inspecting the HTTP request for suspicious patterns, it intercepts the actual operations: the SQL query before it executes, the system command before it runs, the file path before it’s opened, the HTML string before it’s rendered.
This changes what’s detectable. A SQL injection rule in a perimeter WAF fires when it sees an injection pattern in a query parameter, probabilistically. An in-app interceptor fires when it sees an actual injection attempt in the SQL statement being sent to the database driver. It knows the exact statement, the exact method, and whether the input would have caused harm. No guessing.
The practical consequences:
- No false positives on SQLi detection. If the interceptor sees a legitimate SQL statement, it allows it. If it sees an injected query, it blocks it. The distinction is made at the execution level, not the pattern level.
- No tuning required for injection detection. The rule isn’t “block requests matching this pattern.” The rule is “block query execution if the statement structure has been altered by user input.”
- Complete forensic context. When an attack is detected, you get the exact line of code, the exact method, the payload, and the confidence level. This feeds back into your vulnerability management process with precision that perimeter WAF logs can’t match.
- No infrastructure dependency. In-app protection integrates into the application itself. It works regardless of your infrastructure topology: on-premise, multi-cloud, serverless, containers, edge functions.
ByteHide Monitor implements this model across nine attack categories: SQL injection, NoSQL injection, XSS, path traversal, command injection, SSRF, LDAP injection, XXE, and LLM prompt injection. The integration requires no code changes to existing application logic.
In .NET:
// Program.cs (ASP.NET Core)
builder.Services.AddByteHideMonitor(options =>
{
options.ProjectId = "your-project-id";
// Interceptors operate at the execution layer, not the HTTP layer.
// SQLi interception fires before ADO.NET / EF Core executes the query.
// No WAF rules, no pattern matching on request URLs.
options.Interceptors.SqlInjection.Enable();
options.Interceptors.CommandInjection.Enable(); // Before Process.Start()
options.Interceptors.XSS.Enable(); // Before HTML output
options.Interceptors.PathTraversal.Enable(); // Before File I/O
options.Interceptors.SSRF.Enable(); // Before outbound HTTP
options.Interceptors.LlmPromptInjection.Enable(); // Before LLM API calls
options.Actions.OnDetection = DetectionAction.Block | DetectionAction.Log;
});In Node.js:
// app.js (Express)
const { ByteHideMonitor } = require('@bytehide/monitor');
const monitor = new ByteHideMonitor({
projectId: 'your-project-id',
interceptors: {
// Intercepts the actual SQL string before it reaches the database driver.
// Detection is based on query structure, not HTTP request patterns.
sqlInjection: { enabled: true, action: 'block' },
xss: { enabled: true, action: 'block' },
ssrf: { enabled: true, action: 'block' },
pathTraversal: { enabled: true, action: 'block' }
}
});
app.use(monitor.middleware());Perimeter WAF and in-app protection address different parts of the problem. A perimeter WAF filters traffic volume at scale, handles DDoS mitigation, enforces geo and IP policies, and blocks large categories of known-bad traffic before it reaches your application servers. An in-app WAF has precision where it matters most: at the point in the code where an exploit would actually cause damage.
The teams that build the most resilient application security postures don’t choose one over the other. They understand what each layer can and cannot do, and deploy them accordingly. The RASP vs In-App WAF vs Perimeter WAF comparison breaks down the architectural distinctions in more detail if you want to think through where each layer fits in your stack.
FAQ
What is the difference between a WAF rule and a WAF policy?
A WAF rule is a single condition-action pair: “if request matches condition X, take action Y.” A WAF policy is a collection of rules grouped together and applied to a specific application, endpoint, or traffic segment. Policies let you apply different rule sets to different parts of your application. For example, stricter rules on your authentication endpoints and more permissive rules on your static asset paths.
How many WAF rules do I need to protect my application?
There’s no correct number. A well-configured WAF with a managed rule set (typically 200–500 rules covering the OWASP Top 10) plus 10–20 targeted custom rules for your application-specific requirements is a reasonable baseline for most applications. Adding more rules doesn’t improve protection if they cover attack classes that already have adequate coverage, and it increases the false positive surface area.
How do I test WAF rules without affecting production traffic?
The standard approach is to enable the WAF in detection mode (log-only) first and observe what rules would have triggered on real production traffic. For proactive testing, use a dedicated WAF testing tool that sends attack payloads to your staging environment. Before switching to prevention mode, verify both that known attacks are blocked and that your known-good traffic flows are not affected.
Can WAF rules prevent zero-day attacks?
Managed WAF rules protect against known attack patterns. A zero-day exploit using a novel technique that doesn’t match any existing rule will bypass pattern-based detection. Anomaly-based detection (behavior-based rules that flag unusual request patterns regardless of specific payloads) provides partial coverage, but it’s not reliable against sophisticated targeted attacks. Defense-in-depth is the practical answer: application-level protections, dependency scanning, and runtime monitoring.
What is the difference between managed rules and custom rules?
Managed rules are maintained by the WAF vendor or standards body (like OWASP CRS) and protect against known generic attack classes across all web applications. They’re updated as new attack patterns are discovered. Custom rules are written by your security team to protect your application’s specific attack surface: custom endpoints, business logic constraints, IP allowlists, and rate limits tailored to your traffic patterns. Both are necessary: managed rules for broad coverage, custom rules for application-specific requirements.