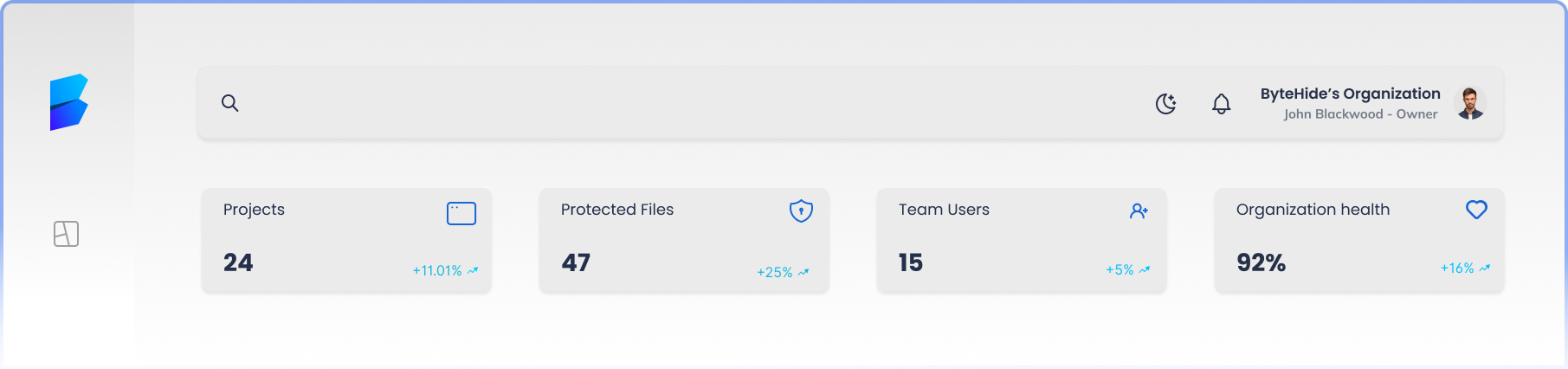
Centralize and manage your secrets securely
Identify, manage and automate exposed code secrets in just one tool with ByteHide Secrets.
Fortify your Secrets, minimize your effort
One single platform to identify, manage and automate exposed code secrets without cybersecurity knowledge needed.
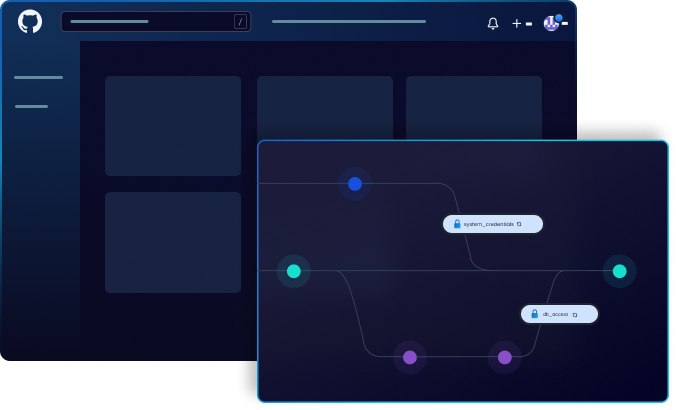
Secrets Rotation
Integration with CI/CD systems to update rotated secrets in applications, thus improving security and reducing the risk of human error in deployment environments.
End-to-End Encryption
Advanced encryption to ensure that secrets are protected both in transit and at rest. We use robust cryptographic algorithms to maintain confidentiality and data integrity.

Local Encrypted Vault
Encrypted local storage of secrets for environments without internet access. Provides an additional layer of security and accessibility in isolated environments.
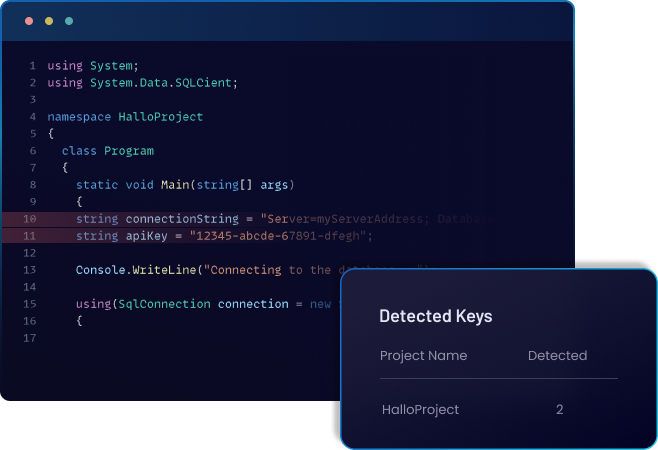
AI-Powered Detection
Utilize artificial intelligence algorithms to detect patterns and potential secret leaks. Continuous system improvement through machine learning to identify emerging threats.
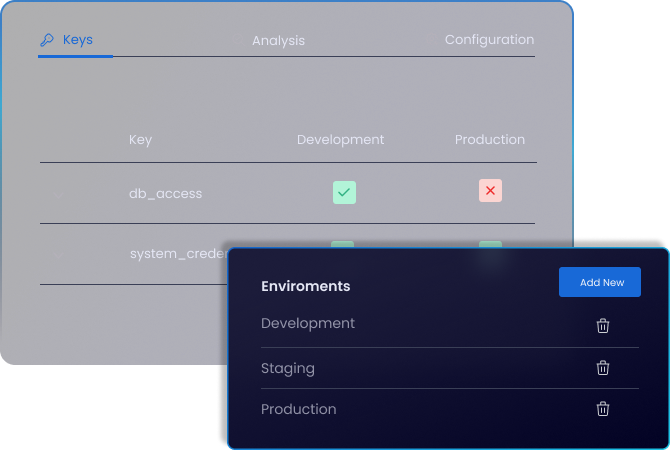
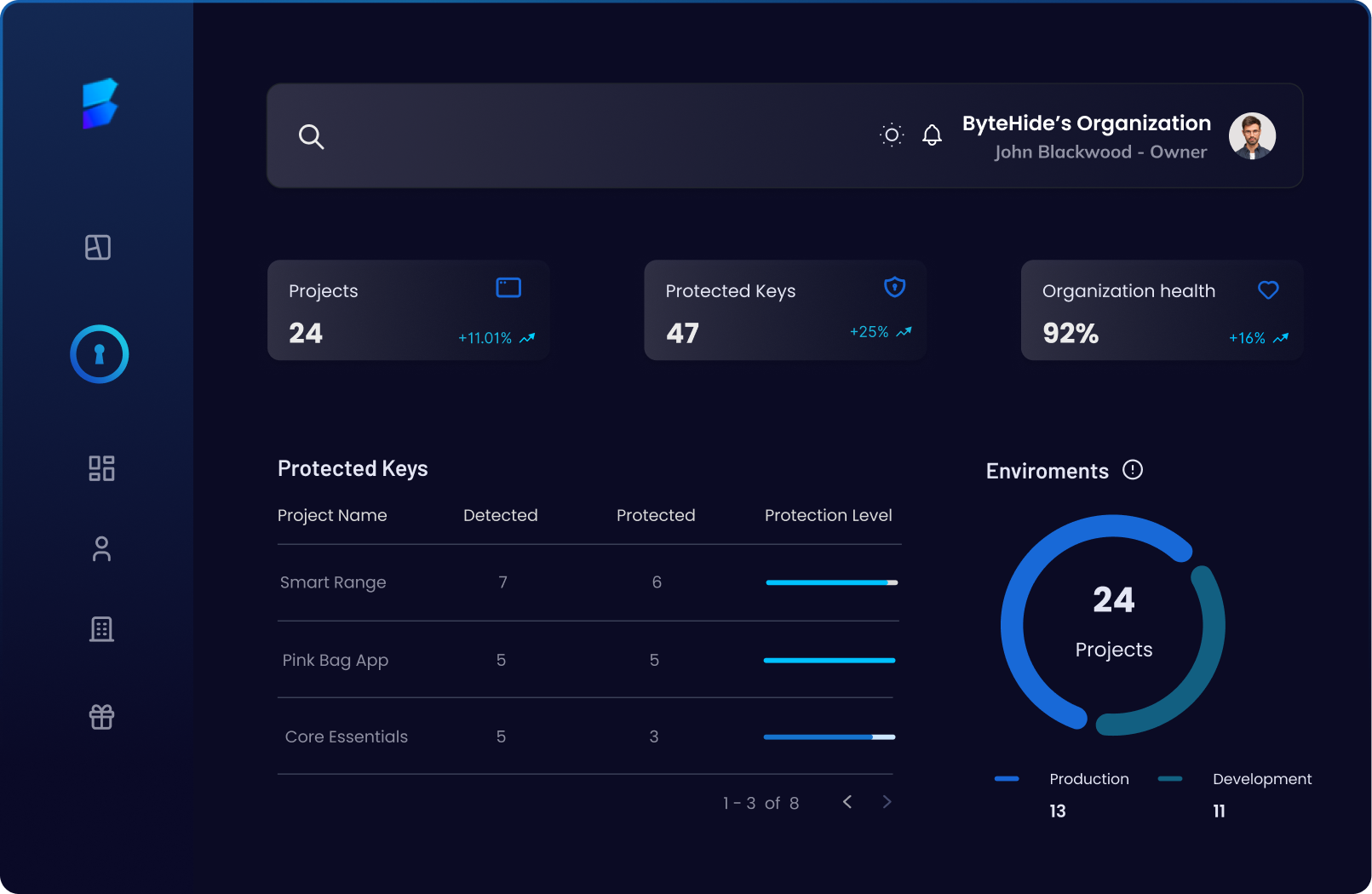
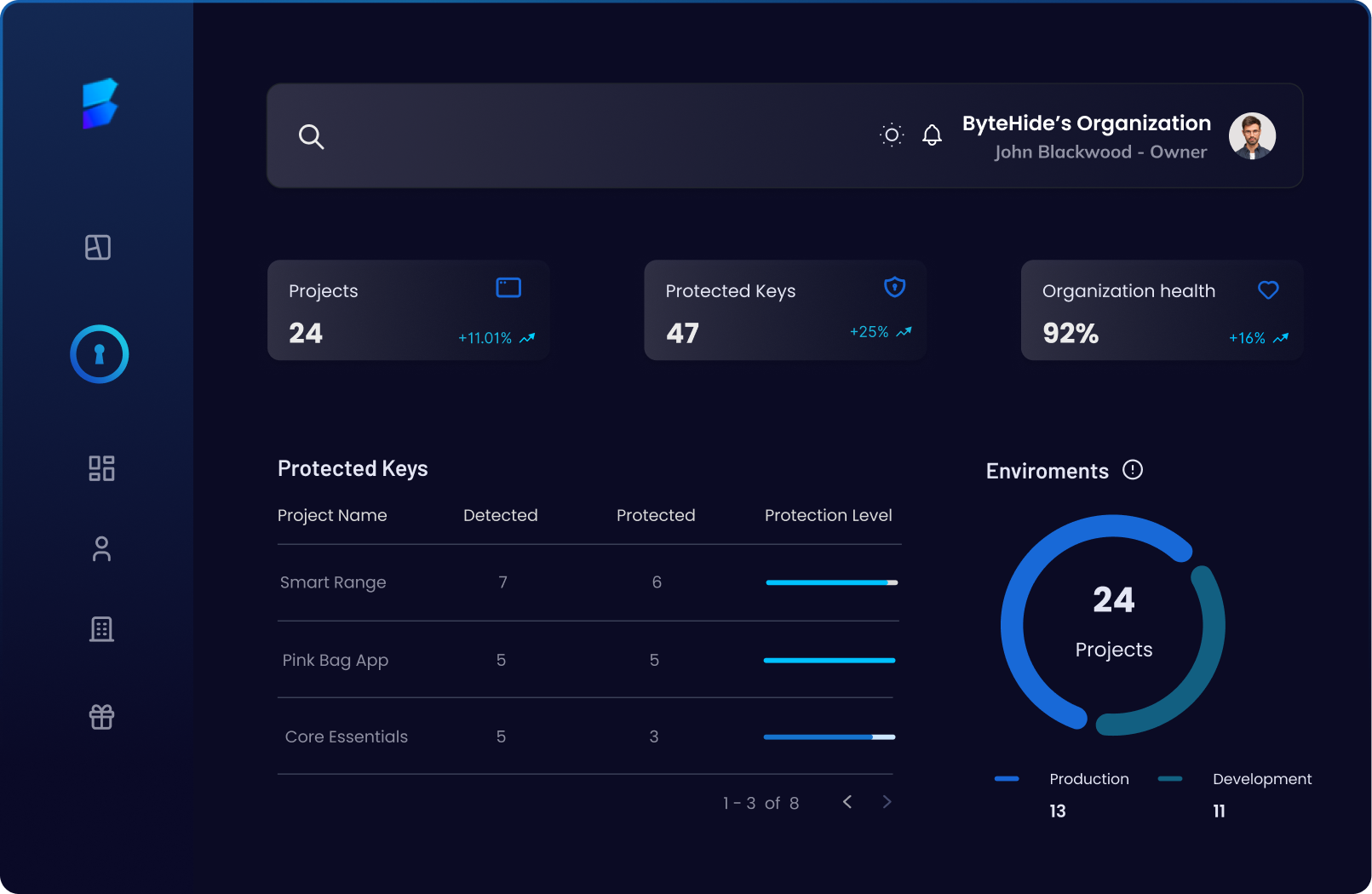
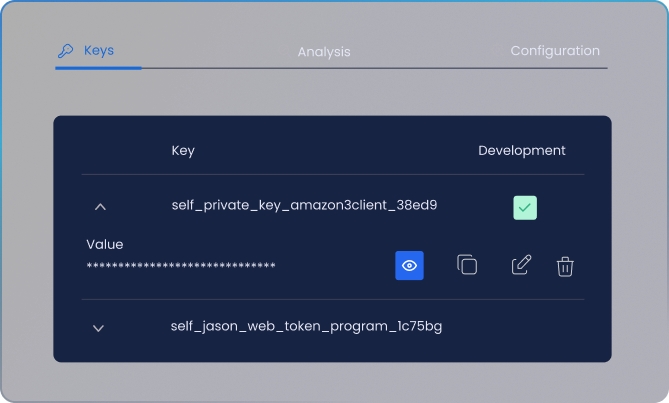
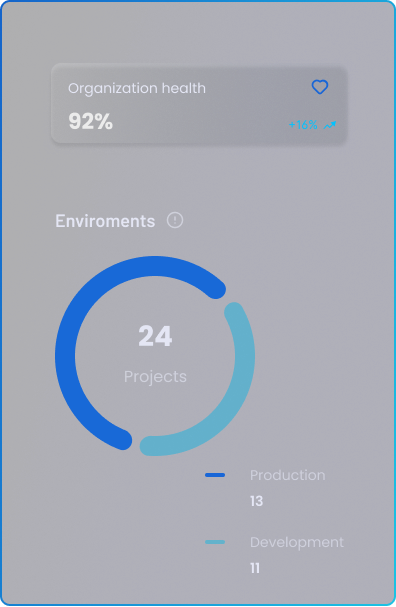
Multiple Environments
Flexible configuration of multiple environments, ensuring centralized and efficient management of secrets in different phases of the software lifecycle.
Fortify your Secrets, minimize your effort
One single platform to identify, manage and automate exposed code secrets without cybersecurity knowledge needed.

Secrets Rotation
Integration with CI/CD systems to update rotated secrets in applications, thus improving security and reducing the risk of human error in deployment environments.
End-to-end encryption
Advanced encryption to ensure that secrets are protected both in transit and at rest. We use robust cryptographic algorithms to maintain confidentiality and data integrity.

Local Encrypted Vault
Encrypted local storage of secrets for environments without internet access. Provides an additional layer of security and accessibility in isolated environments.
AI-Powered Detection
Utilize artificial intelligence algorithms to detect patterns and potential secret leaks. Continuous system improvement through machine learning to identify emerging threats.
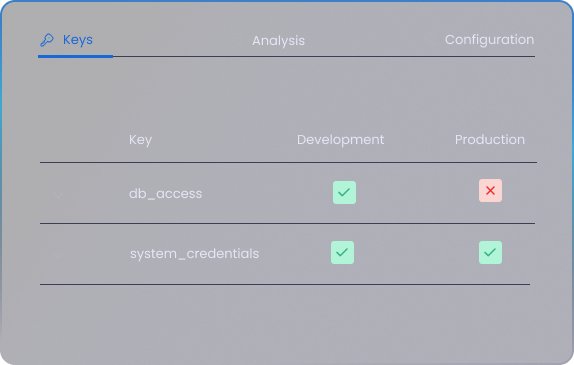
Multiple Environments
Flexible configuration of multiple environments, ensuring centralized and efficient management of secrets in different phases of the software lifecycle.
How it works
Secure your Secrets in 3 simple steps
Integrate in your application
Integrate Secrets adding a nuget package.
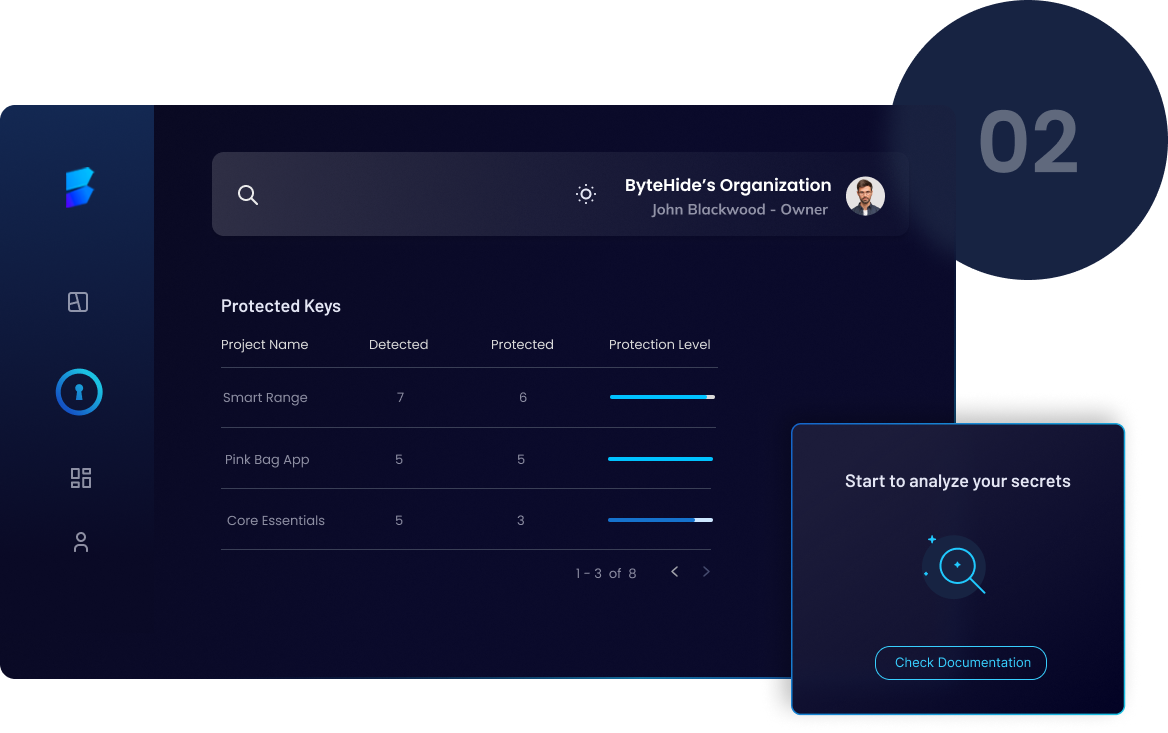
Scan and protect your secrets
During compilation extract automatically the secrets and sync your vault.
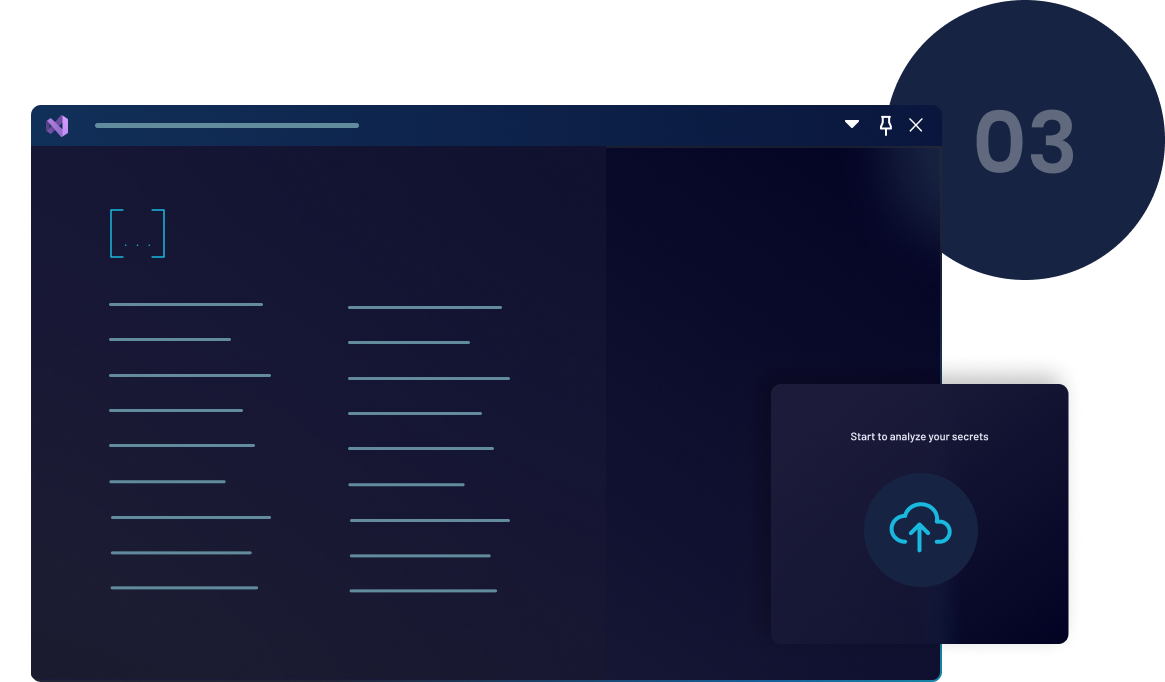
Deploy your application secure
Publish your application without sensitive data in the code.
In-App Shielding and Hardening
Features for Complete Protection
Protect your code at different stages and secure your applications ensuring robust mobile app security throughout the development lifecycle.
- Secure
Storage - Access
Management - Secrets
Editor - Versioning
and recovery - Secrets
Synchronization - Notifications
and Alerts
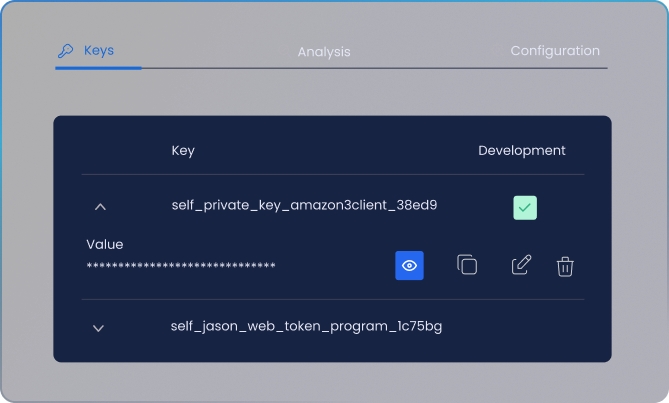
Secure Storage
Store passwords, API keys, OAuth tokens, and certificates in
a secure and encrypted enviroment.

Access Management
Role-Based Access Control (RBAC) to determine who can view
and modify certain secrets.

Secrets Editor
Our editor is built specifically for developers from the ground up.
It offers exceptional speed, incredible flexibility and safeguards
against unintentional interruptions.

Versioning and recovery
Each version of a secret is automatically recorded. Swiftly return to a
previous version to recover from a disruption.

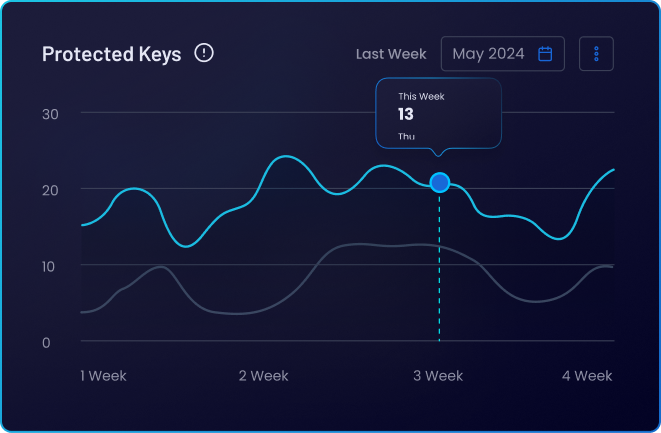
Secrets Synchronization
Real-time analysis of code and repositories to detect
secret exposures as they occur.

Notifications and alerts
Configurable alerts to notify developers when exposed secrets are detected in the code. Secrets expiration notifications to keep them updated.

In-App Shielding and Hardening
Features for Complete Protection
Protect your code at different stages and secure your applications ensuring robust mobile app security throughout the development lifecycle.

Secure Storage
Store passwords, API keys, OAuth tokens, and certificates in a secure and encrypted enviroment.

Access Management
Role-Based Access Control (RBAC) to determine who can view and modify certain secrets.

Secrets Editor
Our editor is built specifically for developers from the ground up. It offers exceptional speed, incredible flexibility and safeguards against unintentional interruptions.

Versioning and recovery
Each version of a secret is automatically recorded. Swiftly return to a previous version to recover from a disruption.

Secrets Synchronization
Real-time analysis of code and repositories to detect secret exposures as they occur.

Notifications and alerts
Configurable alerts to notify developers when exposed secrets are detected in the code. Secrets expiration notifications to keep them updated.


WHY CHOOSE OUR SECRET MANAGER
What makes us different?
Automatic Secrets Synchronization (Sync)
Manually Mark Secrets
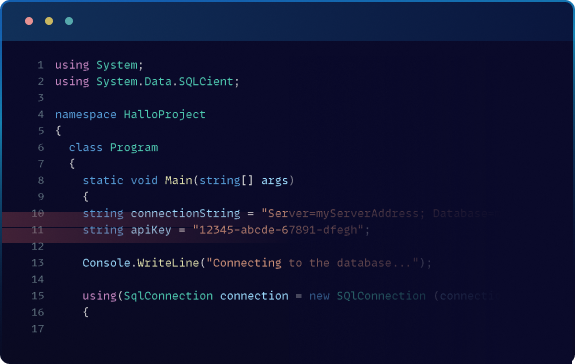
Secrets Detection
Analyzer that scans the source code for exposed secrets. Detailed reports indicating the location and type of secrets found.
Integration with Development Tools
SDKs and APIs to easily integrate the secrets manager with existing applications and services. Plugins for popular IDEs that simplify secrets management during development.
Easy to Use
No technical knowledge is required to protect your sensitive information. User-friendly UI for adding, updating, and deleting secrets. Clear visualization of all stored secrets and their details.
Business Impact
Gain significant
competitive
advantages
over your
competitors
Reduced Risk of Security Breaches
Regulatory Compliance
Effective Security Strategy
Comprehensive Security
Company Reputation Protection
Executive Responsibility
Frequently asked questions
What are secrets?
Secrets are sensitive information needed for authenticating access to different services, such as passwords, API keys, OAuth tokens, and certificates. They are crucial for secure communication between applications, databases, and servers.
This is done to protect your intellectual property, avoid reverse engineering, and safeguard sensitive logic within your software. By using obfuscation techniques, you can make it significantly harder for malicious entities to decompile or tamper with your code.
What is a Secrets Manager?
A Secrets Manager is a software that securely stores, updates, deletes, and integrates secrets, similar to how a password manager works for individuals. It ensures that secrets are handled safely and are always up-to-date without being hard-coded into the application.
Why should I manage and protect my app secrets?
Managing and protecting app secrets:
- Prevent accidental exposure.
- Reduce security vulnerabilities.
- Ensure compliance with data protection regulations.
- Secure secrets management safeguards sensitive information, thus protecting your application and user data.
Does ByteHide Secrets have access to my sensitive data?
No, ByteHide cannot access your secrets under any circumstances. Your secrets are encrypted and can only be accessed with a unique key linked to your account and project. ByteHide provides tools for secure storage and management, but it cannot see the actual content of your secrets.
Do I need high-level knowledge to use ByteHide Secrets?
No, you don’t need advanced knowledge. ByteHide Secrets is designed to be user-friendly with an easy-to-use interface and simple integration tools, making it easy to manage and protect your secrets.