Most organizations running web applications have two security layers in place: a network firewall at the perimeter, and a web application firewall in front of the app. On paper, the coverage looks solid. The network firewall handles unauthorized traffic at the network level. The WAF filters malicious HTTP requests before they reach the server. And yet, web application breaches keep happening to organizations with both.
The reason is architectural, not operational. A web application firewall vs network firewall comparison reveals two tools protecting two different layers, but neither of them protects the layer where modern attacks actually execute: inside the application runtime.
This article breaks down exactly what each layer covers, what it structurally cannot see, and what that gap looks like in practice. The third layer, the In-App Firewall, closes that gap. By the end, you’ll have a precise map of which attack types each layer handles, and which ones pass through both unchallenged.
The Standard Security Stack: WAF + Network Firewall
The WAF + network firewall combination became the default application security stack for a reason: it covers the two most obvious threat surfaces. The network firewall prevents unauthorized access to internal infrastructure. The WAF stops known web attack patterns before they reach the application code.
For organizations running static websites or simple server-rendered applications, this stack is often sufficient. The attacks they face (automated scanners, SQL injection with standard payloads, XSS in URL parameters) are precisely what WAFs were built to catch.
But modern applications are different. APIs handle business logic that differs per user, per session, per endpoint. Applications integrate with LLMs, databases, external services, and file systems. The number of places where malicious input can cause damage has expanded well beyond what HTTP-level filtering was designed to inspect.
The gap isn’t a misconfiguration. It’s a consequence of where these tools sit in the stack.
What a Network Firewall Sees (and What It Can’t)
A network firewall is a security device that monitors and controls traffic based on IP addresses, ports, and protocols. It operates at Layers 3 and 4 of the OSI model, acting as the barrier between untrusted external networks and the internal infrastructure. Next-generation firewalls (NGFWs) extend this with deep packet inspection, application awareness, and intrusion prevention systems, but the fundamental operating layer remains the network.
What a network firewall does well:
- Segmentation. Controls which internal segments can communicate with each other. An application server should not have direct access to your HR database, and the NGFW enforces that boundary.
- Port and protocol control. Blocks services that should not be publicly accessible. Only ports 80 and 443 reach the web server.
- IP-level blocking. Drops traffic from known malicious IP ranges, specific geolocations, or flagged addresses.
- Stateful inspection. Tracks the state of active connections to detect anomalies at the packet level.
- Volumetric DDoS. Absorbs or rate-limits floods of traffic at the network layer before they saturate the application infrastructure.
The structural limit is precise: the network firewall does not understand HTTP semantics. It sees that a packet is going to port 443. It cannot know whether the HTTPS body inside that packet contains a SQL injection payload, a normal search query, or a prompt designed to manipulate a language model. The content is encrypted at the transport layer. Even with TLS inspection enabled on an NGFW, decrypting and re-encrypting at scale introduces latency and operational complexity, and the inspection is still limited to network-level heuristics, not application context.
| What the network firewall sees | What it doesn’t see |
|---|---|
| Source and destination IP | Content inside HTTPS bodies |
| Port and protocol | HTTP method semantics |
| Packet headers and state | SQL queries being constructed |
| Connection patterns | Business logic parameters |
| Known malicious IPs/ranges | Application session context |
| Traffic volume anomalies | Payloads inside encrypted tunnels |
The NGFW adds useful context. It can identify that traffic belongs to a specific application, detect intrusion signatures at the network layer, and apply threat intelligence. But it cannot tell you whether the user_id parameter in a POST body is about to trigger a privilege escalation. That requires understanding the application.
What a WAF Protects (and Where It Goes Blind)
A web application firewall closes the gap the network firewall cannot cover. It operates at Layer 7, decrypting HTTPS traffic (either through SSL offloading or reverse proxy), inspecting the HTTP request content, and filtering requests that match known attack patterns. SQL injection signatures, XSS payloads in URL parameters, path traversal sequences, malformed headers: these are the attacks WAFs were designed to catch.
A WAF also handles threats that have no equivalent at the network layer: bot mitigation based on behavioral patterns, rate limiting per endpoint, geographic blocking at the application level, and DDoS protection for Layer 7 floods like HTTP request floods that pass network-layer checks.
For attacks with recognizable signatures in the HTTP request itself, WAFs perform well. The problem is that a significant class of modern attacks does not have a recognizable signature at the HTTP layer. Three categories account for most of the gap.
Gap 1: Business Logic Attacks
A business logic attack exploits the intended functionality of an application, using valid requests to produce unintended outcomes. The HTTP request looks completely normal: well-formed headers, valid content type, parameters within expected formats. The malicious intent only becomes apparent when the application processes the input.
Consider a scenario where an API accepts a discount_code parameter. A WAF sees a string value. It has no idea whether that discount code is supposed to apply once per account or whether the application has a flaw that allows it to be applied repeatedly. It cannot inspect whether role=manager in a request body is a parameter the application should trust from an unauthenticated endpoint. There is no pattern to block. The attack is in the logic, not the syntax.
OWASP Top 10 2021 lists Broken Access Control (A01) as the number one web application risk. Business logic exploitation is a primary mechanism behind access control failures, and it is invisible to perimeter tools.
Gap 2: Encoded and Obfuscated Payloads
WAFs rely on pattern matching against known attack signatures. Attackers have had decades to study those patterns and develop evasion techniques. Encoding transforms a recognizable payload into something the WAF’s ruleset does not match, while the application server decodes it back to the original form.
Some common encoding approaches that bypass signature-based WAF rules:
- Double URL encoding: Characters encoded twice. The WAF sees encoded characters; the server decodes twice before processing.
- Unicode normalization: Equivalent characters represented differently. The WAF pattern does not match; the application normalizes to the standard form.
- Function-based construction: Instead of writing a payload directly, an attacker constructs it using database string functions.
[injection_payload]assembled fromCHAR()calls does not match a literal keyword scan but executes identically once the database engine evaluates the expression. - Comment insertion: Inline comments in SQL (
/**/) break up keywords that WAF patterns scan for as contiguous strings, while the query parser ignores the comments.
The decode happens inside the application or database engine, a layer the perimeter WAF cannot reach after the request has passed inspection.
Gap 3: LLM Prompt Injection
OWASP Top 10 for LLM Applications lists prompt injection as the number one risk for applications that integrate large language models. A WAF has no mechanism to detect it.
The structural reason is precise: a prompt injection attack lives inside a normal-looking POST body. No SQL keywords, no script tags, no path traversal sequences. The malicious content is natural language text, the same format as a legitimate user query. The WAF sees a string and allows it through. The damage occurs when that string reaches the LLM runtime, where it attempts to override system prompts, exfiltrate context, or manipulate model behavior.
Detecting prompt injection requires semantic understanding of the input in the context of the model being called. That analysis can only happen inside the application, at the point where the input is passed to the LLM. In my experience, teams integrating LLMs are often the last to realize their WAF provides zero coverage for this attack class.
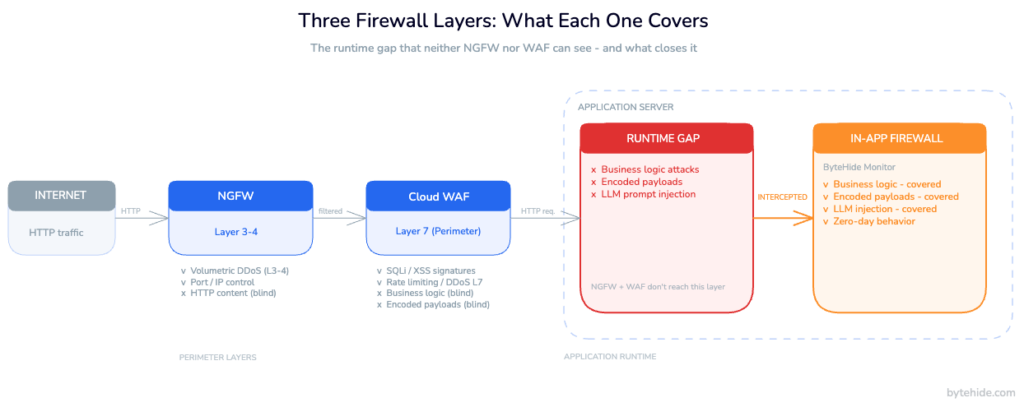
The Gap Neither Layer Covers
Visualizing the actual gap helps clarify what tools belong in it. Between the perimeter WAF (which inspects the incoming HTTP request) and the network firewall (which inspects the packet), there is a layer those tools never see: the interior of the application at execution time.
Specifically, neither layer can observe:
- The SQL query being dynamically constructed from parameters that individually passed WAF inspection. The query might be malicious. The WAF saw clean input going in; it did not see the query going out.
- The call to
Process.Start()with arguments assembled from a URL parameter that contained no recognizable injection syntax. The NGFW sees outbound traffic to a subprocess. It does not know how the argument was constructed. - The file path passed to a read operation where the path came from user input, traversed within the expected directory structure, and only reveals a sensitive file because the application has a logic flaw.
- The outbound HTTP request generated by SSRF, triggered by a parameter that pointed to an internal metadata endpoint. The WAF checked the incoming request. It did not check where the application made requests as a result.
- The deserialized object from a JSON body that looked benign as raw bytes, but executes arbitrary code when the application’s deserialization logic processes it.
This is not a list of exotic edge cases. These are categories from OWASP Top 10 2021 — specifically A01 Broken Access Control, A03 Injection (in its modern forms), A08 Software and Data Integrity Failures, and A10 Server-Side Request Forgery. They represent the attack surface that perimeter tools structurally cannot cover, because the damage point is inside the runtime, not at the border.
What Is an In-App Firewall?
An In-App Firewall is a security layer embedded inside the application runtime as middleware or an SDK, intercepting function calls at the exact point where an attack would execute: the SQL statement about to be sent to the database driver, the OS command about to be passed to the process manager, the template about to be rendered, the prompt about to be forwarded to the language model.
This is the key architectural difference from perimeter tools. A cloud WAF inspects the incoming HTTP request and makes a binary allow-or-block decision based on what the request looks like from the outside. An In-App Firewall intercepts the internal operation the request triggered and makes a decision based on what the application is actually about to do.
The practical consequences are significant.
False positive rate drops. The In-App Firewall does not guess whether a parameter is malicious by matching it against patterns. It knows whether that parameter actually reached a database query or an OS call. If it didn’t, there is nothing to block, regardless of what the parameter looked like.
Business logic attacks become detectable. The In-App Firewall understands the application’s execution context. It can detect that a route which normally performs read operations is being used to trigger a write, or that a parameter combination produces an anomalous code path.
Encoded payloads no longer evade detection. By the time the In-App Firewall intercepts the database call, the application has already decoded the input. The firewall sees the final, decoded operation, not the encoded form that the perimeter WAF scanned.
LLM prompts can be inspected in context. An In-App Firewall operating at the function call where the prompt is passed to the model can analyze the input semantically, detecting role manipulation attempts, delimiter injection, and system prompt extraction patterns before they reach the LLM.
The conceptual predecessor of In-App Firewalls is RASP (Runtime Application Self-Protection). Traditional RASP implementations carried a reputation for high performance overhead and complex deployment, which limited adoption. Modern In-App Firewalls are lightweight middleware packages with sub-millisecond overhead per request, and deployment is a dependency installation plus two lines of initialization code.
In Node.js (Express):
// npm install @bytehide/monitor
const { monitor } = require('@bytehide/monitor');
app.use(monitor.protect({ projectToken: 'YOUR_PROJECT_TOKEN' }));
// Intercepts SQLi, NoSQLi, XSS, SSRF, Command Injection, Path Traversal,
// LLM Prompt Injection, and more — at the execution layer, not the HTTP layerIn .NET (ASP.NET Core):
// dotnet add package ByteHide.Monitor
builder.Services.AddByteHideMonitor("YOUR_PROJECT_TOKEN");
app.UseByteHideMonitor();
// Intercepts at ADO.NET/EF Core driver level, Process.Start(), and template renderers
// Syncs rules from cloud dashboard — no redeploy required for rule updatesNo infrastructure changes. No DNS rerouting. No proxy configuration. The firewall initializes with the application and operates inside the same process. For teams running microservices, serverless functions, or containerized workloads (architectures where there is no single perimeter to defend) this deployment model is the only practical option for application-layer protection.
For teams that want to understand runtime security and runtime threat detection more broadly, these concepts describe the same operating environment where In-App Firewalls work.
What Each Firewall Type Catches: A Complete Attack Coverage Table
The table below maps common attack types against the three firewall layers. The goal is not to argue that one layer replaces another. It is to show precisely which attacks each layer handles, which it handles partially, and which fall entirely outside its scope.
| Attack Type | Network Firewall / NGFW | WAF (Perimeter) | In-App Firewall |
|---|---|---|---|
| Volumetric DDoS (Layer 3-4) | ✅ Absorbs at network layer | ⚠️ Layer 7 DDoS only | ❌ Not designed for this |
| Port scanning / network intrusion | ✅ | ❌ | ❌ |
| SQL injection (standard payload) | ❌ | ✅ Pattern matching on HTTP | ✅ Intercepts the actual query |
| SQL injection (encoded/obfuscated) | ❌ | ⚠️ Depends on rule coverage | ✅ Sees the decoded final statement |
| XSS (reflected, URL parameter) | ❌ | ✅ | ✅ Before template render |
| Business logic abuse | ❌ | ❌ | ✅ Application context available |
| Command injection | ❌ | ⚠️ Partial pattern matching | ✅ Intercepts Process.Start() |
| SSRF | ❌ | ⚠️ Blocks known internal ranges | ✅ Intercepts outbound HTTP calls |
| Path traversal | ❌ | ✅ Detects ../ patterns | ✅ Intercepts file system calls |
| LLM prompt injection | ❌ | ❌ | ✅ Intercepts before model call |
| Zero-day (behavioral anomaly) | ❌ | ❌ Signature-dependent | ✅ Behavioral analysis at runtime |
✅ Direct protection | ⚠️ Partial, depends on configuration or payload form | ❌ Outside architectural scope
The pattern is consistent. Network firewalls own Layers 3-4. WAFs own standard HTTP-layer attack signatures. In-App Firewalls own the runtime execution layer, and that is the only layer that sees all three categories of gap attacks: business logic, encoded payloads, and semantic threats like prompt injection.
Frequently Asked Questions
What is the difference between a WAF and a network firewall?
A network firewall operates at Layers 3-4 of the OSI model, filtering traffic by IP address, port, and protocol. It has no visibility into HTTP content or application logic. A web application firewall operates at Layer 7, inspecting HTTP and HTTPS requests and filtering patterns associated with web attacks like SQL injection and XSS. Next-generation firewalls extend the network layer with some application awareness and deep packet inspection, but they cannot inspect encrypted application payloads or understand the application’s internal logic. The two tools protect different threat surfaces and are complementary, not interchangeable.
Can a network firewall replace a WAF?
No. A network firewall can block entire ports and protocols, but it cannot distinguish a legitimate HTTPS request from a malicious one at the application level. If you need to allow web traffic while filtering SQL injection, XSS, and other HTTP-layer attacks, you need a WAF. Conversely, a WAF does not replace network-level segmentation and port control. Each tool covers a layer the other cannot.
What attacks can bypass both a WAF and a network firewall?
Business logic attacks, encoded or obfuscated payloads that decode inside the database engine, privilege escalation via valid-looking parameters, SSRF triggered by internal application logic, and LLM prompt injection can all pass through both perimeter layers. These attacks use HTTP requests that contain no recognizable malicious signatures. The attack manifests inside the application runtime when the code processes the input. Detecting them requires visibility into what the application does with the input, not just what the input looks like.
What is an In-App Firewall?
An In-App Firewall is a security layer embedded inside the application process as middleware or an SDK. Instead of inspecting HTTP requests at the network perimeter, it intercepts internal function calls at the point of execution: the SQL query about to run, the OS command about to execute, the file path about to be opened, the prompt about to be sent to a language model. Because it operates inside the application context, it can detect attacks that perimeter tools structurally cannot see, including business logic abuse, encoded payloads, and LLM prompt injection.
Do I need all three layers network firewall, WAF, and In-App Firewall?
For modern API-first and microservices applications, yes. Each layer covers a threat surface the others cannot reach. The network firewall handles network-level segmentation and volumetric threats. The WAF handles standard HTTP-layer attacks and DDoS at Layer 7. The In-App Firewall handles the runtime execution layer business logic, encoded payloads, semantic attacks. Static websites and simple server-rendered applications can often operate adequately with just the first two layers. Applications with APIs, dynamic business logic, LLM integrations, or multi-service architectures need all three for complete coverage.
For organizations evaluating In-App Firewall options, ByteHide Monitor implements this pattern as middleware for Node.js and .NET applications, with rule synchronization from a cloud dashboard and no infrastructure dependency.
The debate about whether a web application firewall or network firewall is sufficient belongs to an earlier era of web architecture. Static pages, monolithic servers, predictable request patterns: perimeter tools were built for that world and they worked. Modern applications generate server-side behavior dynamically from user input, integrate with external AI systems, and run across distributed infrastructure with no single perimeter. The security layer that matches that architecture operates where the code runs.