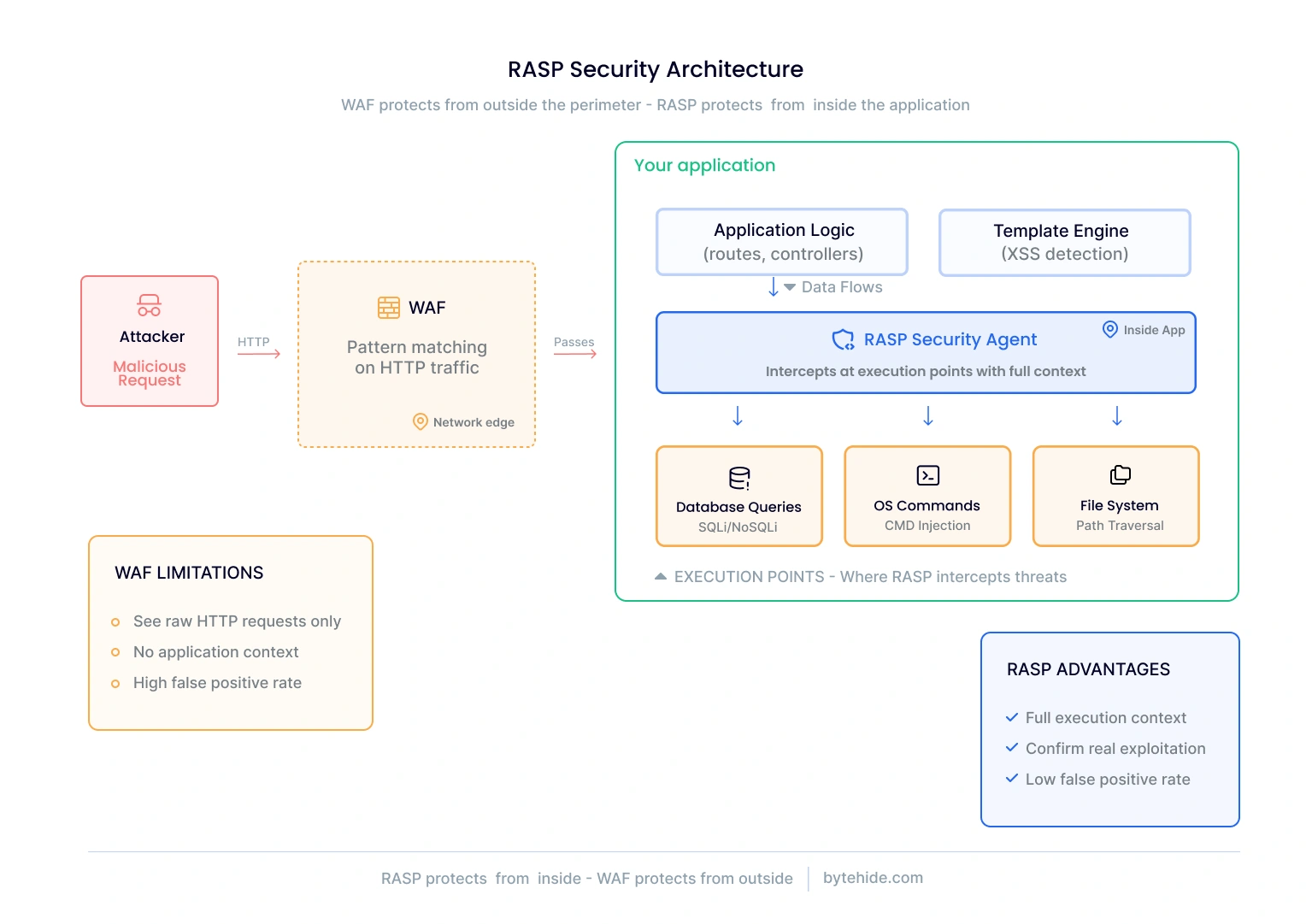
Most application security tools work from the outside. Firewalls inspect traffic at the network edge. Static analyzers scan source code before deployment. Vulnerability scanners probe applications from the perspective of an attacker. All of these approaches share a blind spot: none of them can see what actually happens inside your application when it processes a request.
RASP security takes a fundamentally different approach. Instead of guarding the perimeter, a RASP agent runs inside your application, watching how data flows through your code and intercepting threats at the exact point where they would cause damage. The concept was first defined by Gartner in 2012, and it has since become a critical layer in modern application security architectures.
This article explains what RASP security is, how it works at a technical level, the specific attack types it detects, how it compares to other security approaches, and how the technology is evolving beyond its original design.
What Is RASP Security?
RASP (Runtime Application Self-Protection) is a security technology that embeds directly inside an application to detect and block attacks in real time during execution. Unlike perimeter defenses that analyze traffic externally, RASP operates within the application’s runtime environment, giving it full visibility into how data moves through code paths, database queries, system commands, and API calls.
The term was coined by Gartner analyst Joseph Feiman in 2012 to describe a then-emerging category of security tools that could make applications “self-protecting.” The core idea is straightforward: instead of relying on external systems to guess whether a request is malicious based on patterns, let the application itself confirm whether an attack is actually reaching a vulnerable execution point.
In practice, RASP works by hooking into critical functions within your application: the database driver, the command execution layer, the file system interface, the template engine. When user input reaches one of these functions, the RASP agent evaluates whether that input constitutes a real threat based on the full execution context, not just the surface-level HTTP request.
This is why it’s called “self-protection.” The application doesn’t depend on an external firewall or scanner to defend it. The security logic lives inside the app itself, travels with it across environments (cloud, on-prem, containerized), and protects it regardless of the network topology.
How Does RASP Work?
Runtime application self-protection operates through instrumentation of the application’s runtime environment. A lightweight agent or SDK integrates into the application, typically requiring only a few lines of configuration rather than changes to business logic.
Once active, the RASP agent monitors specific execution points where security-sensitive operations occur. The interception flow works like this:
- A user sends a request to your application
- Your application processes the request through its normal logic
- When the processed data reaches a critical operation (a database query, an OS command, a file read, a template render), the RASP agent intercepts
- The agent evaluates the data in context: is this input actually forming a malicious SQL statement? Is this string genuinely attempting command injection? Or is it benign data that just happens to contain special characters?
- Based on the analysis, the agent either allows the operation, blocks it, or logs it for review
The difference from a WAF is significant. A WAF sees the raw HTTP request and tries to pattern-match against known attack signatures. It has no idea whether a suspicious-looking string will actually reach a vulnerable code path. RASP confirms the threat at the execution point itself.
Most RASP solutions support two operational modes. Detection mode (also called monitoring or alert-only) logs potential threats without blocking them. This lets teams understand their application’s behavior and tune the detection before enabling active protection. Blocking mode intercepts and prevents attacks in real time. In my experience, teams should always start in detection mode for at least a few days before switching to blocking, especially in high-traffic production environments.
Modern RASP implementations also use confidence scoring. Not every suspicious pattern warrants the same response. A clearly malicious SQL injection attempt with high confidence gets blocked immediately. An ambiguous input that might be a false positive gets logged and flagged. This graduated response reduces the risk of disrupting legitimate traffic.
Here’s what adding RASP protection looks like in practice:
// Node.js — Add runtime protection in 3 lines
const monitor = require('@bytehide/monitor');
monitor.init({ projectToken: 'your-token' });
app.use(monitor.protect());// .NET — Equivalent setup
using ByteHide.Monitor;
var builder = WebApplication.CreateBuilder(args);
builder.Services.AddByteHideMonitor(options => {
options.ProjectToken = "your-token";
});
var app = builder.Build();
app.UseByteHideMonitor(); // Runtime protection activeNo changes to your application logic. The SDK hooks into critical execution points automatically and begins monitoring from the first request.
What Does RASP Detect and Block?
One of the most common questions about RASP security is what it actually protects against. Most guides give a vague answer about “runtime threats.” Here are the specific attack categories that RASP solutions intercept, with how each detection works at the execution level.
SQL Injection. The RASP agent monitors database driver calls. When user input reaches a SQL query, the agent analyzes whether the input modifies the query’s structure (adding UNION SELECT, OR 1=1, or comment sequences) versus simply providing a parameter value. Because the agent sees the actual query being constructed, it catches encoded, fragmented, and second-order injection that perimeter tools miss.
Cross-Site Scripting (XSS). When user-supplied data reaches a template rendering engine or HTML output function, the RASP agent checks whether the content includes executable JavaScript, event handlers, or other XSS vectors. This catches both reflected and stored XSS at the point of output, regardless of how the data entered the application.
Command Injection. Before any operating system command executes through Process.Start(), exec(), or equivalent functions, the RASP agent inspects the command string. If user input has been concatenated into a shell command in a way that allows arbitrary command execution, the agent blocks it.
Path Traversal. File system operations are monitored for directory traversal sequences (../, ..\, encoded variants). The agent verifies that file access stays within the application’s intended scope, preventing attackers from reading configuration files, source code, or system files.
Server-Side Request Forgery (SSRF). When the application makes outbound HTTP requests, the RASP agent checks whether the target URL has been influenced by user input to target internal services, cloud metadata endpoints (169.254.169.254), or other restricted resources.
LDAP Injection. For applications that query directory services, the agent monitors LDAP query construction for injected filter modifications that could expose unauthorized directory data.
XML External Entity (XXE). The agent intercepts XML parsing operations, detecting attempts to define external entities that could read local files, make network requests, or cause denial of service through entity expansion.
NoSQL Injection. MongoDB and other NoSQL database queries are monitored for operator injection ($gt, $ne, $where) that could bypass authentication or extract unauthorized data.
LLM Prompt Injection. This is the newest detection category, and one that no traditional RASP solution was designed for. For applications integrating large language models (OpenAI, Claude, Gemini), the agent inspects prompts before they reach the model, detecting jailbreak attempts, system prompt extraction, role manipulation, and encoded payloads. This addresses what OWASP identifies as the #1 risk for LLM applications.
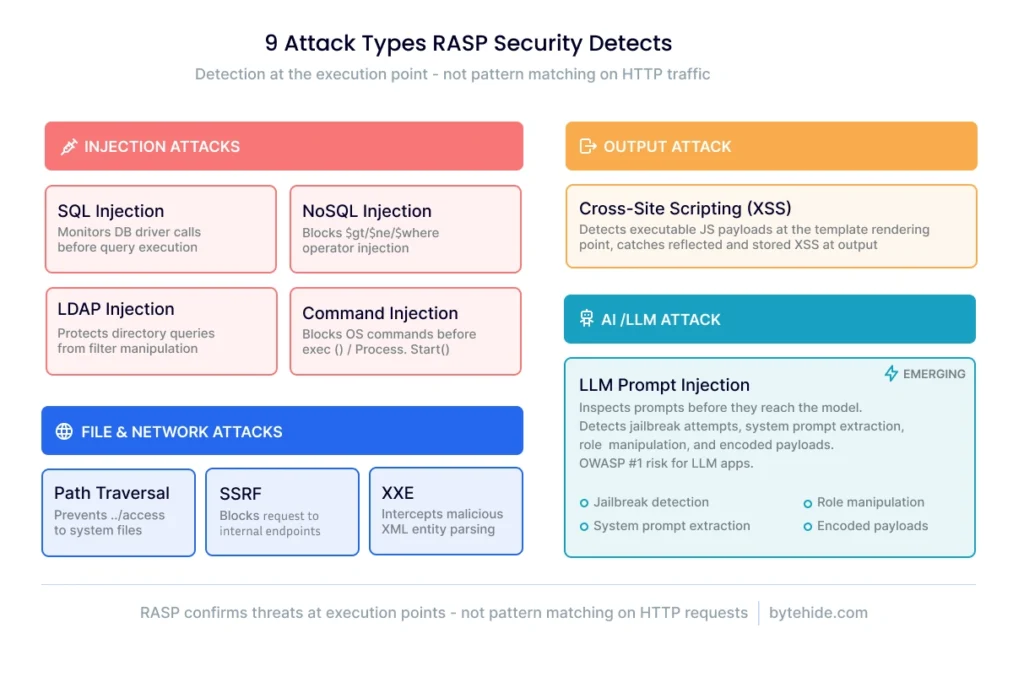
The key distinction across all these detection types: RASP confirms the threat at the execution point. A SQL injection is not flagged because the HTTP request contains a suspicious string. It’s flagged because that string actually reached a database query and would have modified its structure.
RASP vs WAF vs SAST: Key Differences
RASP security is one component of a broader application security strategy. Understanding how it compares to other approaches helps clarify where each fits.
| Criteria | RASP | WAF | SAST |
|---|---|---|---|
| When it runs | Runtime (production) | Runtime (perimeter) | Build-time (CI/CD) |
| Where it operates | Inside the application | Network edge (proxy/CDN) | Source code repository |
| Detection method | Behavioral analysis at execution points | Pattern matching on HTTP traffic | Static pattern matching on code |
| Application context | Full (sees data flow through code) | None (sees only raw requests) | Partial (code only, no runtime behavior) |
| False positive rate | Low (confirms real exploitation) | High (no execution context) | High (no runtime context) |
| Zero-day coverage | Yes (behavioral detection) | Limited (signature-dependent) | No (known patterns only) |
| Performance impact | Varies (agent-dependent) | Minimal on app (external) | None on production |
These three approaches are complementary, not competing. SAST catches vulnerabilities during development before they reach production. WAFs filter high-volume, known attack patterns at the network edge. RASP catches what gets through both layers by confirming exploitation at the code level.
For a deeper analysis of how RASP compares specifically to web application firewalls, including when each approach is the better choice, see our detailed RASP vs WAF comparison.
Benefits of RASP Security
RASP security provides several advantages that other application security approaches cannot replicate, specifically because of its position inside the application.
The most significant benefit is precision. Because RASP confirms attacks at the execution point rather than guessing from HTTP patterns, it produces dramatically fewer false positives than perimeter-based tools. When a RASP agent reports a SQL injection, it means user input actually reached a database query and attempted to modify its structure. This precision translates directly into less time spent investigating false alerts.
Real-time blocking is another core advantage. RASP doesn’t just detect threats after the fact. It intercepts and blocks malicious operations before they complete. An SQL injection is stopped before the query executes. A command injection is blocked before the OS command runs. This is active prevention, not passive detection.
Zero-day coverage follows naturally from behavioral detection. RASP doesn’t rely on signature databases that need to be updated when new vulnerabilities are discovered. It monitors behavior. If an attacker exploits a vulnerability that has never been cataloged, RASP still detects the anomalous behavior (a query being modified, a command being injected) regardless of the specific exploit technique.
RASP also provides forensic depth that network-level tools cannot match. Instead of reporting “suspicious request to /api/users,” a RASP agent reports “attempted SQL injection targeting the getUserById query in UserService, where user input modified the WHERE clause.” This level of detail accelerates both incident response and remediation.
Finally, RASP deploys as part of the application itself. It travels with your code across environments: development, staging, production, cloud, on-premises, containerized. No network reconfiguration, no DNS changes, no infrastructure dependencies.
RASP Challenges and Limitations
No security technology is without tradeoffs, and honesty about limitations builds more trust than marketing claims.
Traditional RASP agents that instrument the entire runtime environment can introduce measurable performance overhead. Full instrumentation of the JVM or CLR adds latency to every function call, which matters in high-throughput APIs where milliseconds count. This has been the primary objection to RASP adoption since the technology’s early days.
Language and framework dependency is another challenge. Most traditional RASP solutions support only one or two runtime environments. A team running Java services, Node.js microservices, and .NET APIs might need three separate RASP solutions, each with its own configuration and management overhead.
Deployment complexity varies significantly between vendors. Some solutions require JVM flags, bytecode manipulation, or middleware configuration that can be invasive. Others deploy as simple SDK installations. The gap in deployment experience across the market is wide.
And RASP is not a standalone security solution. It protects the application layer but doesn’t handle network-level DDoS attacks, doesn’t scan source code for vulnerabilities during development, and doesn’t replace the need for secure coding practices. It is one layer in a defense-in-depth strategy.
These limitations, particularly around performance and deployment complexity, have driven the evolution toward lighter approaches. Modern SDK-based solutions target specific interception points rather than instrumenting the full runtime, reducing overhead to under 1ms per check while maintaining the core benefit of application-context awareness.
RASP for Different Platforms
RASP security is often discussed exclusively in the context of web servers and APIs. But the principle of runtime self-protection applies wherever code executes, and the attack surface extends well beyond the server.
Cloud and web applications represent the traditional RASP use case. .NET and Node.js applications serving APIs and web interfaces face injection attacks, authentication bypasses, and increasingly prompt injection against LLM integrations. This is where RASP matured and where the broadest tooling exists.
Mobile applications face a distinct set of runtime threats. On Android and iOS, attackers attempt runtime tampering, method hooking, debugger attachment, and execution on rooted or jailbroken devices. Mobile RASP detects these manipulation attempts and can respond by terminating the session, wiping sensitive data, or alerting the backend. This is particularly critical for fintech and healthcare applications where regulatory requirements mandate runtime integrity verification.
Desktop applications built on .NET or Electron frameworks process sensitive data locally and are vulnerable to memory inspection, API hooking, and binary patching. Runtime protection for desktop applications monitors process integrity and detects unauthorized modifications during execution.
IoT and embedded devices represent an emerging frontier. Connected devices running application code are increasingly targeted, and their limited update cycles make runtime protection valuable as a compensating control when patching isn’t immediately possible.
The common thread across all platforms: if code executes and processes untrusted input, runtime protection adds a security layer that static analysis and perimeter defenses cannot provide.
The Evolution of RASP: From Heavy Agents to In-App WAFs
RASP has changed significantly since Gartner first defined the category in 2012. Understanding this evolution helps explain both the current state of the technology and where it’s heading.
First-generation RASP solutions relied on deep runtime instrumentation. Java agents modified bytecode at load time. .NET profilers hooked into the CLR. These approaches provided comprehensive visibility but came with real costs: performance overhead, complex deployment, tight coupling to specific runtime versions, and limited cross-platform support.
The second generation moved toward lighter SDK-based architectures. Instead of instrumenting the entire runtime, these solutions target specific execution points: database drivers, command execution functions, file system calls, template engines. This targeted approach reduces overhead significantly while maintaining the core advantage of application-context detection.
The latest evolution combines RASP’s application-context awareness with capabilities traditionally associated with WAFs and threat intelligence platforms. These solutions, sometimes called In-App WAFs, add several layers beyond what traditional RASP provides.
Threat intelligence integration brings databases of 600M+ known malicious IPs and 390+ bot signatures directly into the application layer, enabling blocking decisions based on reputation data without depending on external infrastructure.
Runtime-to-SAST correlation closes a gap that has existed since both tools were invented. When a RASP agent confirms that a specific vulnerability is being actively exploited in production, it can feed that signal back to static analysis tools like ByteHide Radar, automatically reprioritizing that finding from “medium” to “critical.” This means teams fix what attackers are actually targeting, not just what scanners flag.
And LLM prompt injection detection addresses a threat class that didn’t exist when RASP was designed. As more applications integrate language models, runtime inspection of prompts before they reach the model becomes essential security hygiene.
For a detailed comparison of how these approaches differ, see our analysis of RASP vs WAF and the In-App WAF approach.
How to Implement RASP Security
Implementing RASP protection follows a predictable pattern regardless of which solution you choose.
Select your approach. Agent-based solutions instrument the runtime and provide the broadest visibility but come with higher deployment complexity. SDK-based solutions (including In-App WAFs) install as packages and target specific interception points with lower overhead. Your choice depends on your performance requirements, language ecosystem, and operational capacity.
Deploy in detection mode first. This is not optional. Run RASP in monitoring-only mode for at least a week in your production environment. This establishes a baseline of normal application behavior, surfaces any false positives that need tuning, and builds confidence before you enable blocking. Skipping this step is the most common implementation mistake.
Enable blocking gradually. Start by blocking high-confidence detections only (clear SQL injection, obvious command injection). Expand to lower-confidence detections as you verify accuracy. Some teams maintain certain detection categories in monitoring mode permanently, using RASP as a forensic tool rather than an active blocker for edge cases.
Integrate with your existing security stack. RASP generates valuable telemetry. Connect it to your SIEM for centralized alerting. Feed runtime data to your SAST tool to reprioritize static findings based on what’s actually being exploited. Set up automated incident response workflows for high-severity detections.
Monitor and iterate. Runtime security is not set-and-forget. Review detection logs regularly. Tune confidence thresholds as your application evolves. Update interception rules when you add new functionality that processes untrusted input.
If you want to see how SDK-based runtime protection works in practice, explore ByteHide Monitor or start with the free tier.
Frequently Asked Questions
What does RASP stand for in cybersecurity?
RASP stands for Runtime Application Self-Protection. The term was introduced by Gartner in 2012 to describe security technology that embeds directly inside applications to detect and block attacks during execution. Unlike external security tools, RASP operates within the application’s runtime environment, giving it full context into how data is processed.
How is RASP different from a WAF?
A Web Application Firewall operates at the network perimeter, inspecting HTTP traffic using pattern-matching rules before requests reach your application. RASP operates inside the application itself, monitoring code execution and data flow. The key difference is context: a WAF sees raw requests, while RASP sees how those requests are actually processed by your code. This gives RASP lower false positive rates and the ability to catch attacks that bypass WAF rules through encoding or fragmentation. For a detailed comparison, see RASP vs WAF.
Does RASP affect application performance?
It depends on the implementation. Traditional RASP agents that instrument the entire runtime can add measurable latency, particularly in high-throughput environments. Modern SDK-based approaches target specific execution points (database queries, OS commands, file operations) rather than instrumenting everything, typically adding less than 1ms per check. The performance impact should always be benchmarked in your specific environment before enabling blocking mode.
What types of attacks does RASP prevent?
RASP security detects and blocks attacks at the execution point, including SQL injection, cross-site scripting (XSS), command injection, path traversal, server-side request forgery (SSRF), LDAP injection, XML external entity (XXE) attacks, NoSQL injection, and increasingly LLM prompt injection. The common thread is that RASP confirms the threat by observing the actual impact on the application, rather than guessing from HTTP request patterns.
Can RASP replace a WAF?
Not recommended as a complete replacement. RASP and WAFs serve complementary purposes. WAFs are effective at filtering high-volume traffic, blocking known bad actors by IP reputation, and handling DDoS mitigation at the network edge. RASP excels at catching sophisticated attacks that bypass WAF rules, confirming real exploitation, and providing code-level forensic data. For teams that want both capabilities without managing two separate tools, In-App WAF solutions combine perimeter-style filtering with RASP-level application context in a single SDK.
Is RASP only for web applications?
No. While RASP originated in web application and API security, the technology now extends to mobile applications (Android and iOS runtime protection, root/jailbreak detection), desktop applications (.NET runtime integrity monitoring), and IoT devices. The core principle of protecting code during execution applies to any platform where applications process untrusted input.
RASP has come a long way from the heavyweight Java agents that first defined the category. The principle remains sound: the application that processes the data is in the best position to determine whether that data constitutes a threat. What has changed is the implementation. Today’s SDK-based approaches make runtime protection accessible to teams that would never have considered deploying a traditional RASP agent, across platforms that the original technology was never designed to protect. Whether that evolution leads to RASP as a standalone category or gets absorbed into broader runtime security platforms is an open question. But the need for application-layer visibility during execution is only growing.